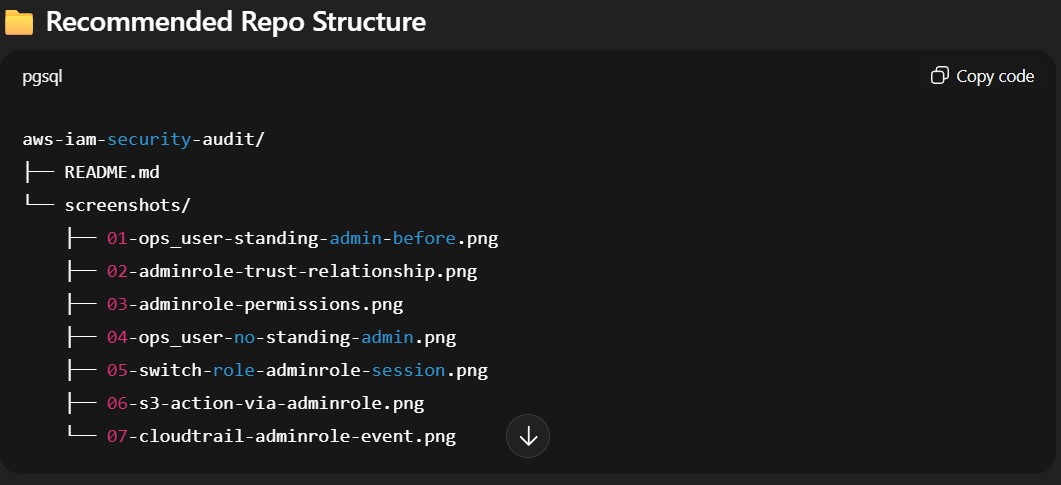
#2 AWS IAM Security Review: Manual Access Audit & Temporary Role Implementation
Overview
This lab demonstrates a hands-on AWS IAM security review focused on identifying and mitigating over-privileged access, enforcing least privilege, and implementing temporary, auditable administrative access using IAM roles and STS — all within a Free Tier, single-account environment.
Environment
- Account Type: Single AWS Account (Free Tier)
- Tools Used: AWS IAM Console, IAM Access Analyzer, AWS CloudTrail
- Scope: IAM Users, Groups, Roles
- Limitations: No AWS Organizations, no paid security services
Objective
- Identify over-privileged IAM users
- Remove unnecessary standing permissions
- Replace persistent admin access with temporary, role-based access
- Ensure actions are auditable and time-bound
- Follow AWS least-privilege and security best practices
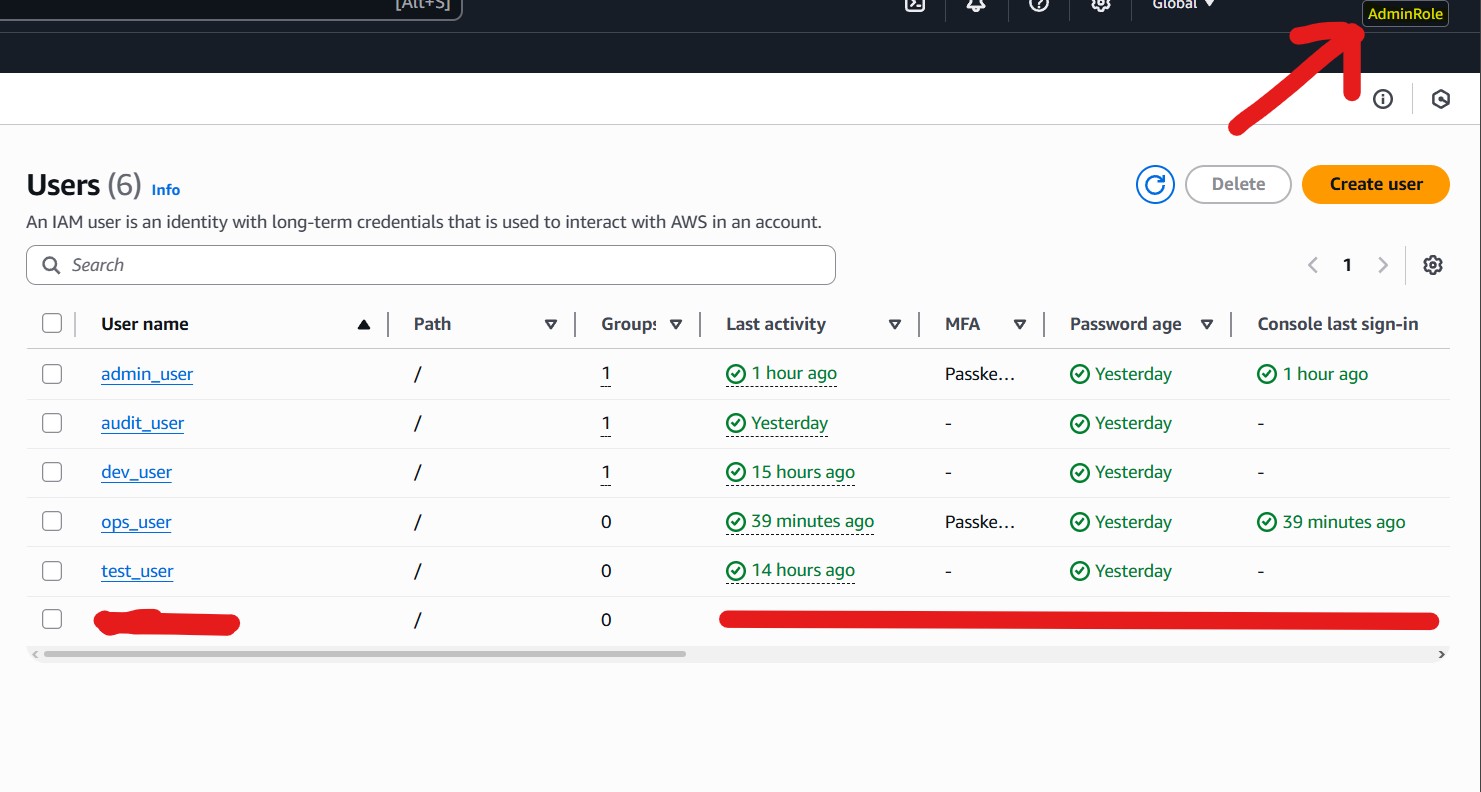
Users in Scope
- admin_user: Standing AdministratorAccess (lab exception)
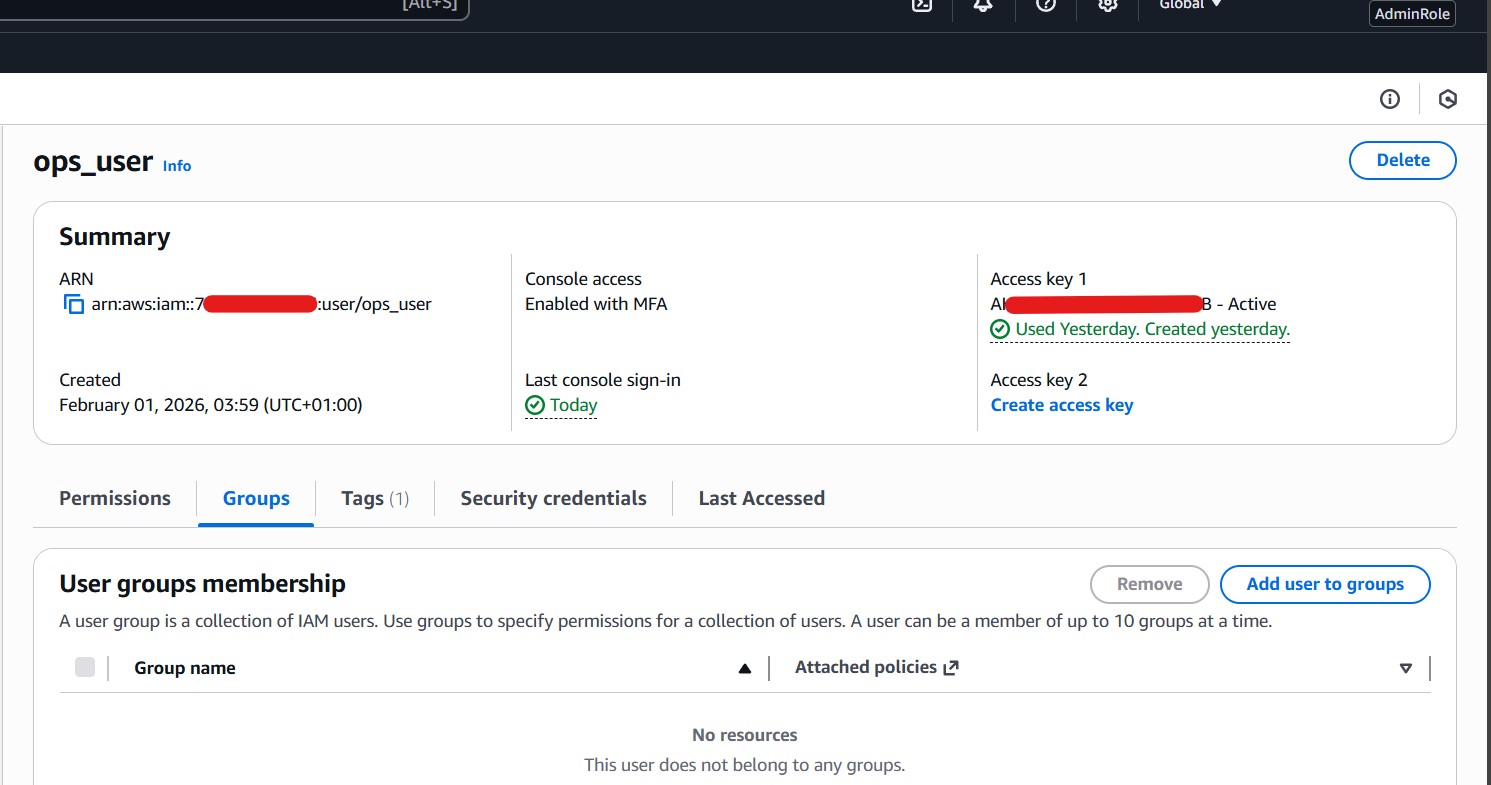
- ops_user: Standing AdministratorAccess (to be removed)
- dev_user: AmazonS3FullAccess + AmazonEC2ReadOnlyAccess
- audit_user: ReadOnlyAccess
- test_user: Orphaned / revoked
Key Steps
- IAM Users & Groups Review
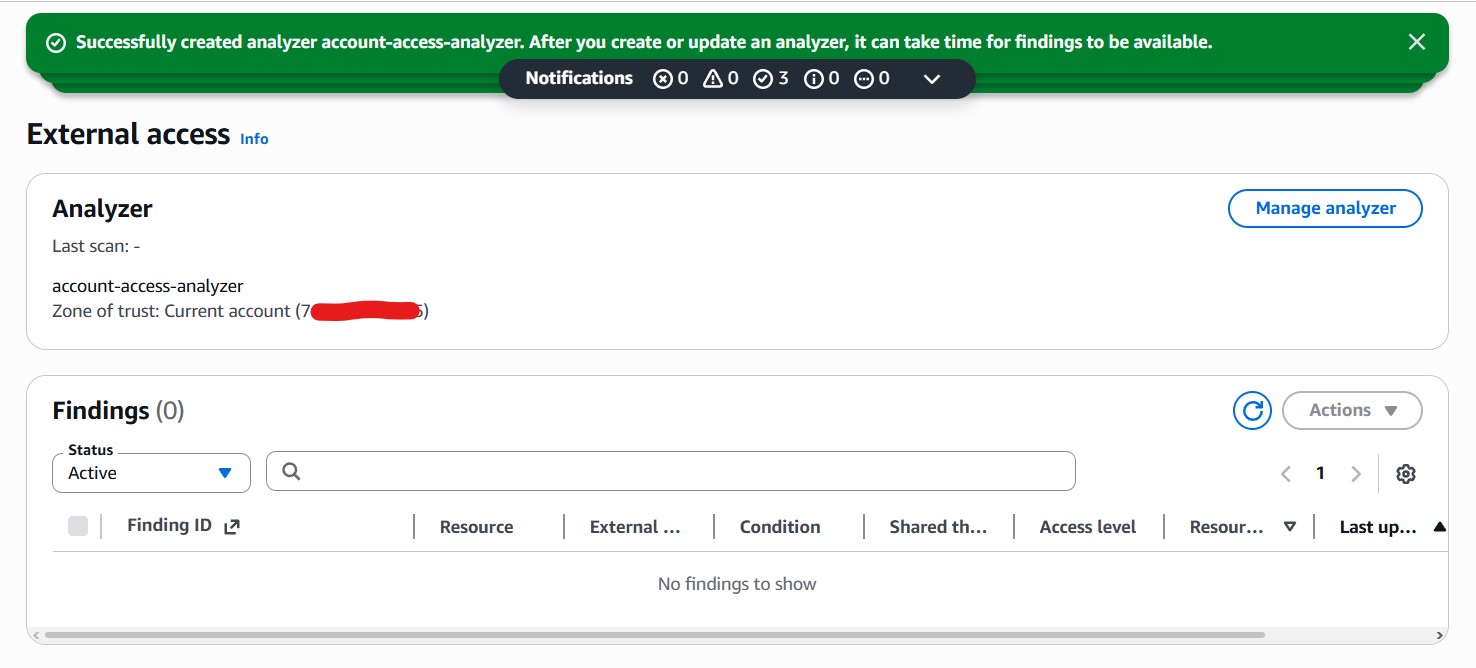
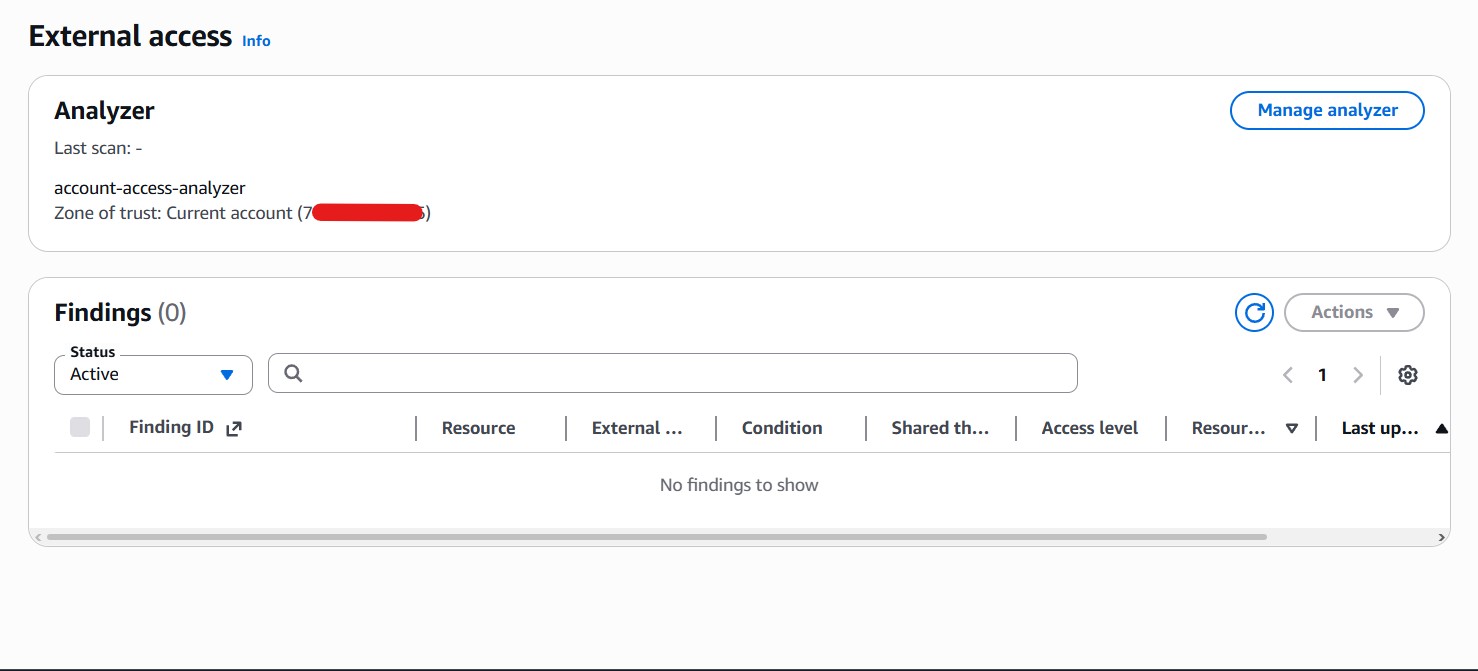
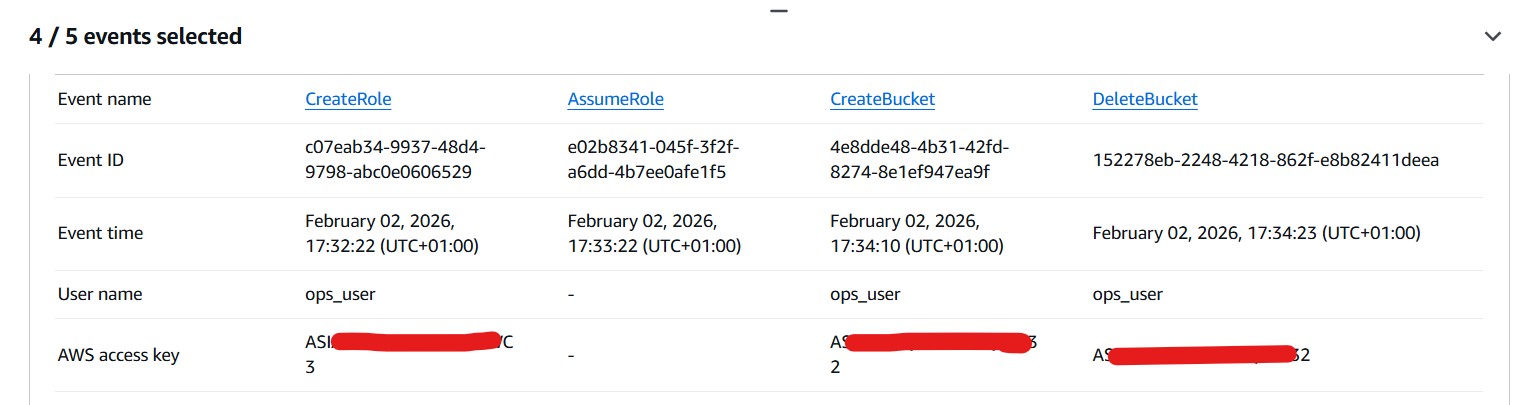
Identified standing admin access on ops_user and admin_user. - Access Analyzer Scan
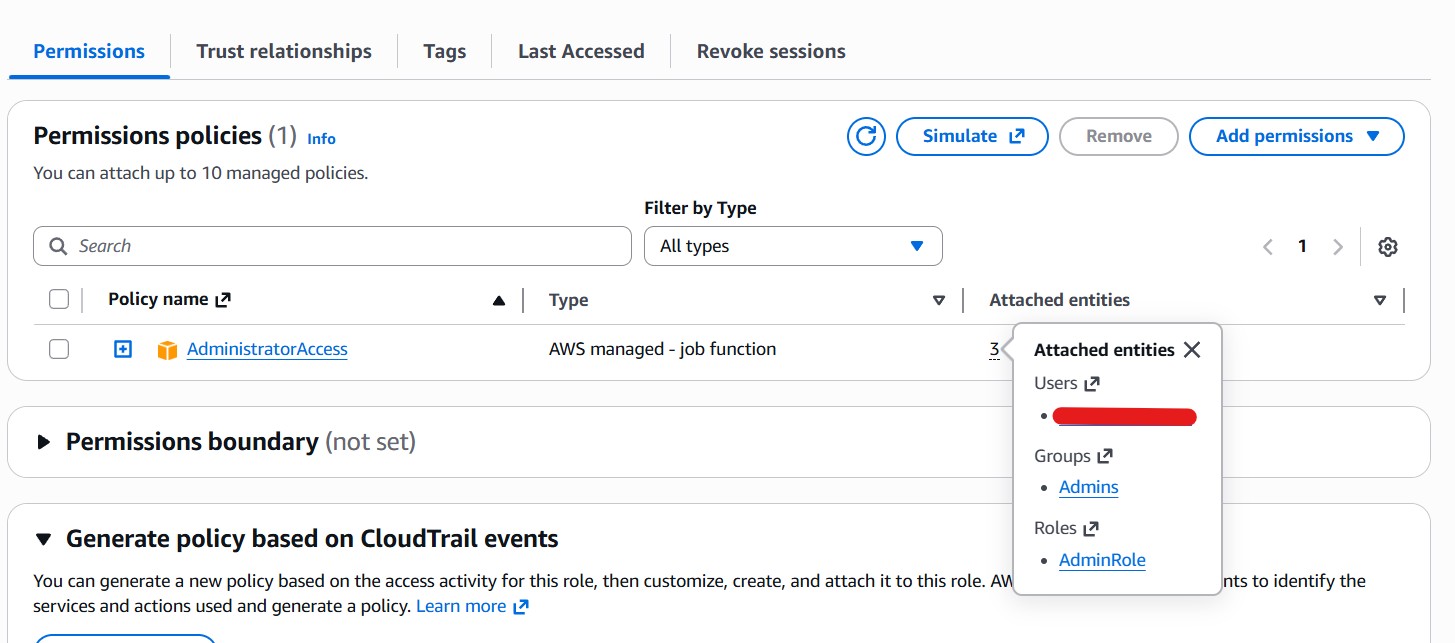
No external access findings; confirmed no unintended permissions. - Temporary Admin Role Creation
AdminRole with AdministratorAccess, trust limited to ops_user, MFA required. - Removal of Standing Admin Access
Detached AdministratorAccess from ops_user (user & group level). - Validation
Assumed AdminRole via Switch Role, tested S3/EC2 actions, confirmed no standing access remains. - Logging & Audit
CloudTrail enabled; verified AssumeRole events and temporary credentials.
Lessons Learned
- IAM users should not hold standing administrative permissions
- Roles + STS significantly reduce blast radius
- Trust policies are as critical as permission policies
- Testing destructive actions validates real-world access
- Enterprise-grade security patterns achievable in Free Tier
"This lab mirrors real-world IAM evolution: from standing user permissions → temporary, auditable role-based access."
Outcome
Standing admin access removed • Temporary role-based access implemented • All actions auditable via CloudTrail • Least privilege enforced • Risks mitigated.
Next Steps
- Automate role assumption & revocation
- Use granular custom policies
- Integrate CloudTrail monitoring & alerts