ACT I — PART 3
AWS IAM Privilege Escalation Case Study
Social Engineering + CLI‑Based PassRole Abuse
Executive Summary
This case study documents a controlled AWS lab exercise demonstrating how IAM misconfigurations involving iam:PassRole can lead to privilege escalation, even when traditional console‑based protections are in place.
The lab highlights a realistic attacker progression:
- Initial access via low‑privileged automation credentials
- Console‑based escalation attempts blocked by IAM hardening
- Pivot to AWS CLI (PowerShell)
- Successful privilege escalation through EC2 role attachment
- Creation of persistent administrator‑privileged infrastructure without lifecycle control
A key outcome is the distinction between browser‑based security controls and programmatic/API threat models — console guardrails alone are insufficient when automation permissions are misaligned.
Lab Objectives
- Demonstrate differences between console‑based and CLI‑based attack surfaces
- Show how
iam:PassRolecan be abused without IAM visibility - Illustrate real‑world social engineering trust failures
- Highlight risks of automation users creating privileged infrastructure
- Emphasize the danger of creation permissions without lifecycle control
Environment Overview
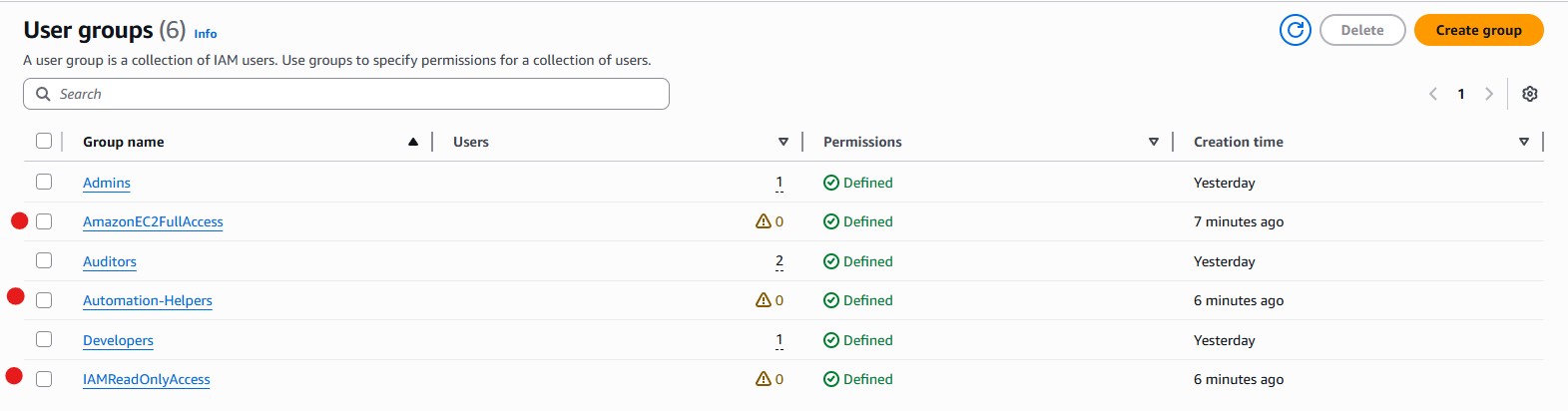
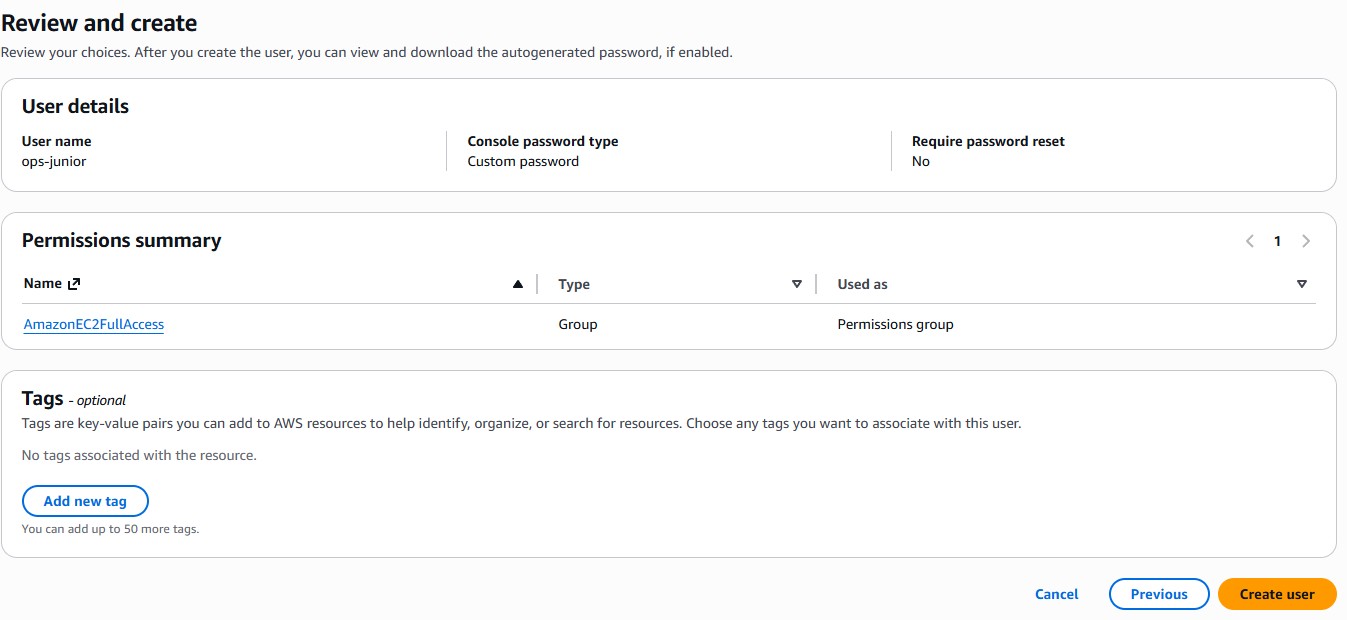
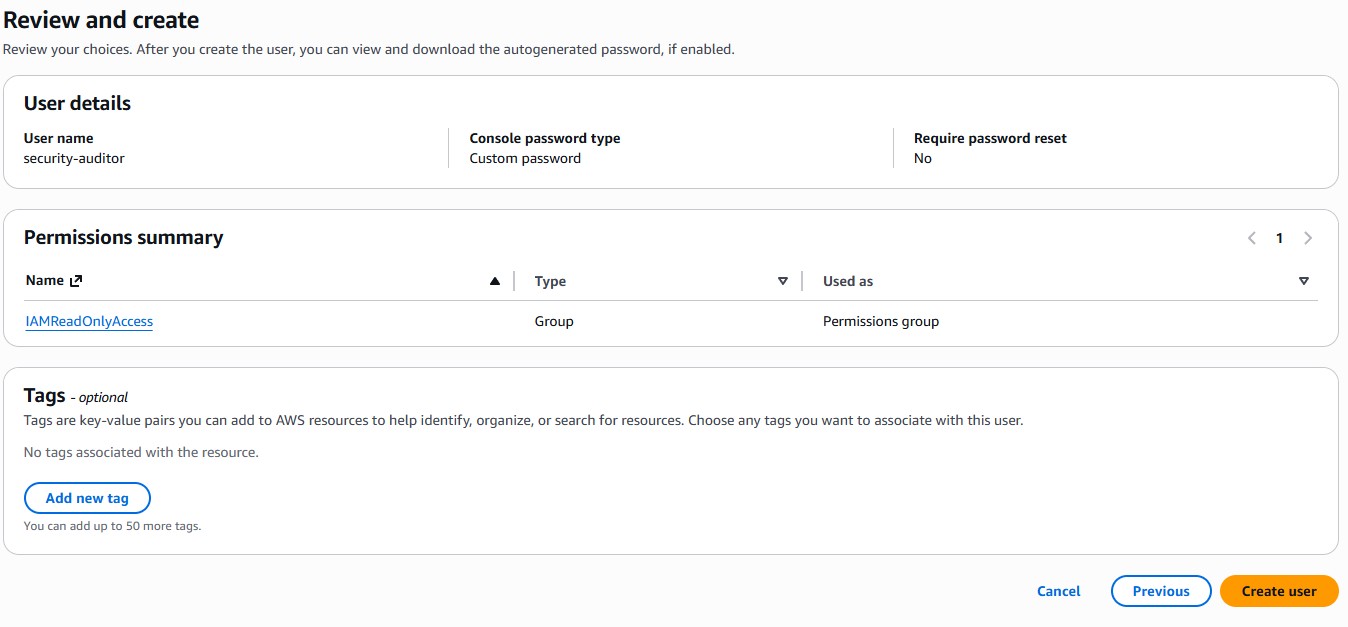
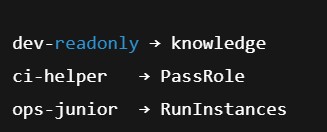
IAM Users
| User | Intended Role |
|---|---|
| ops-junior | Junior operations, EC2 via console |
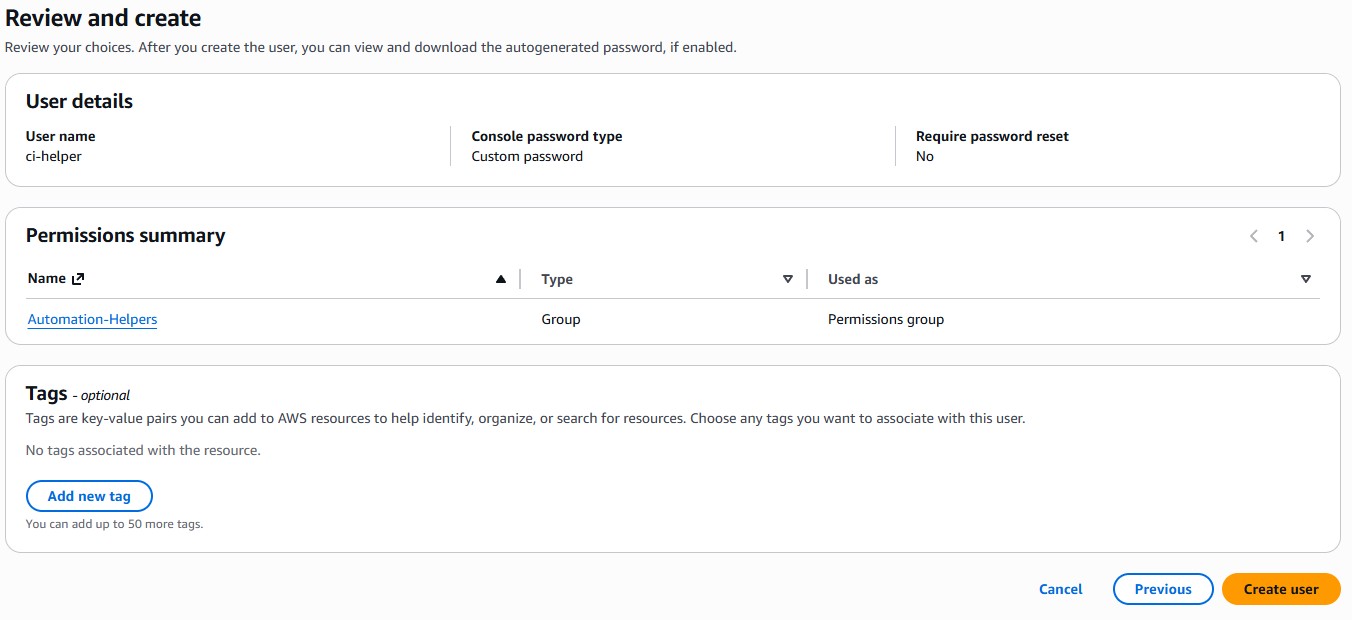
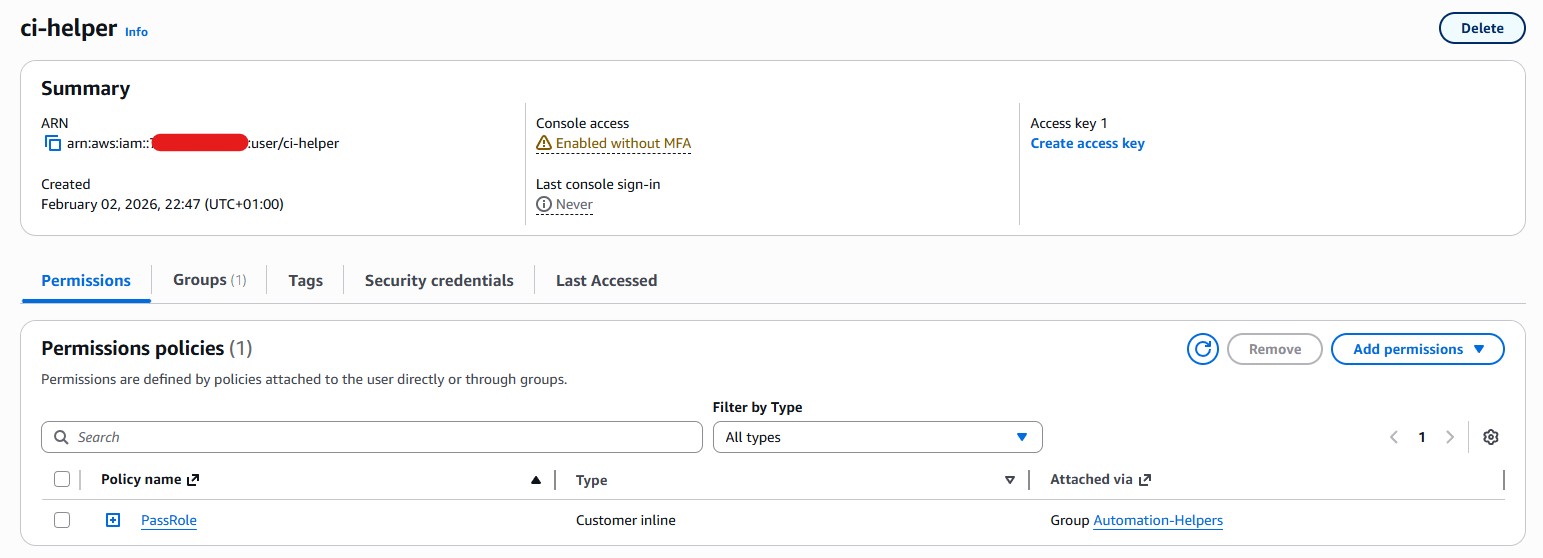
| ci-helper | CI / automation user (CLI access) |
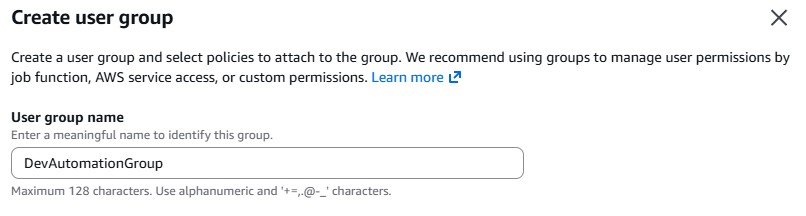
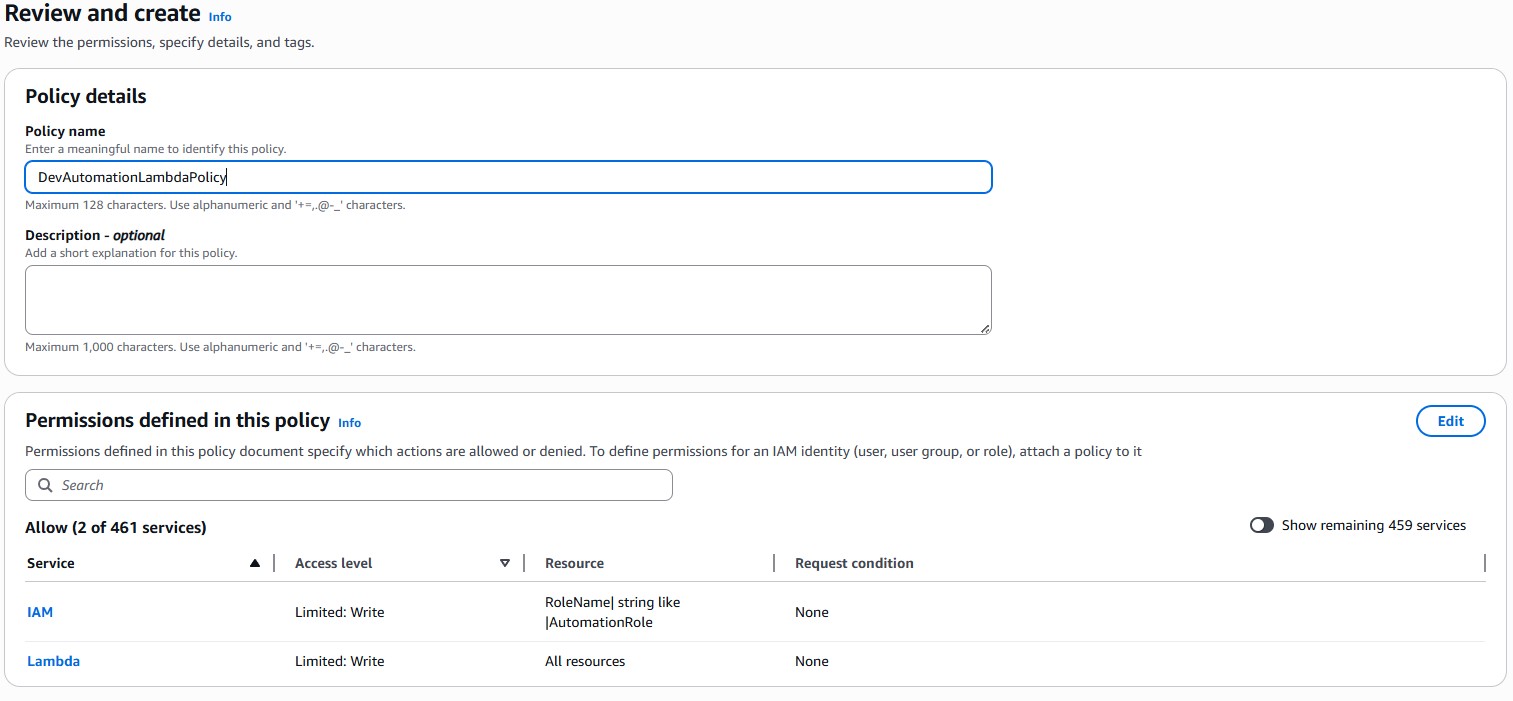
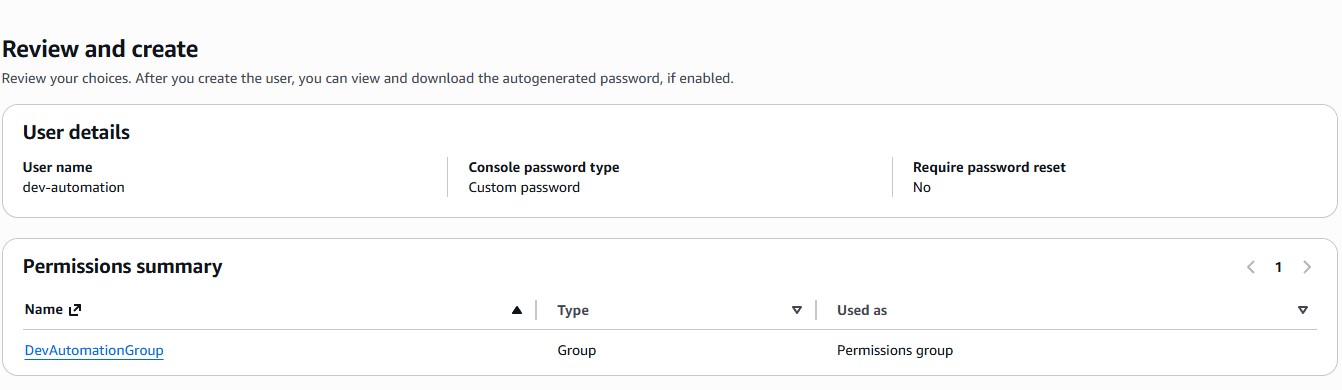
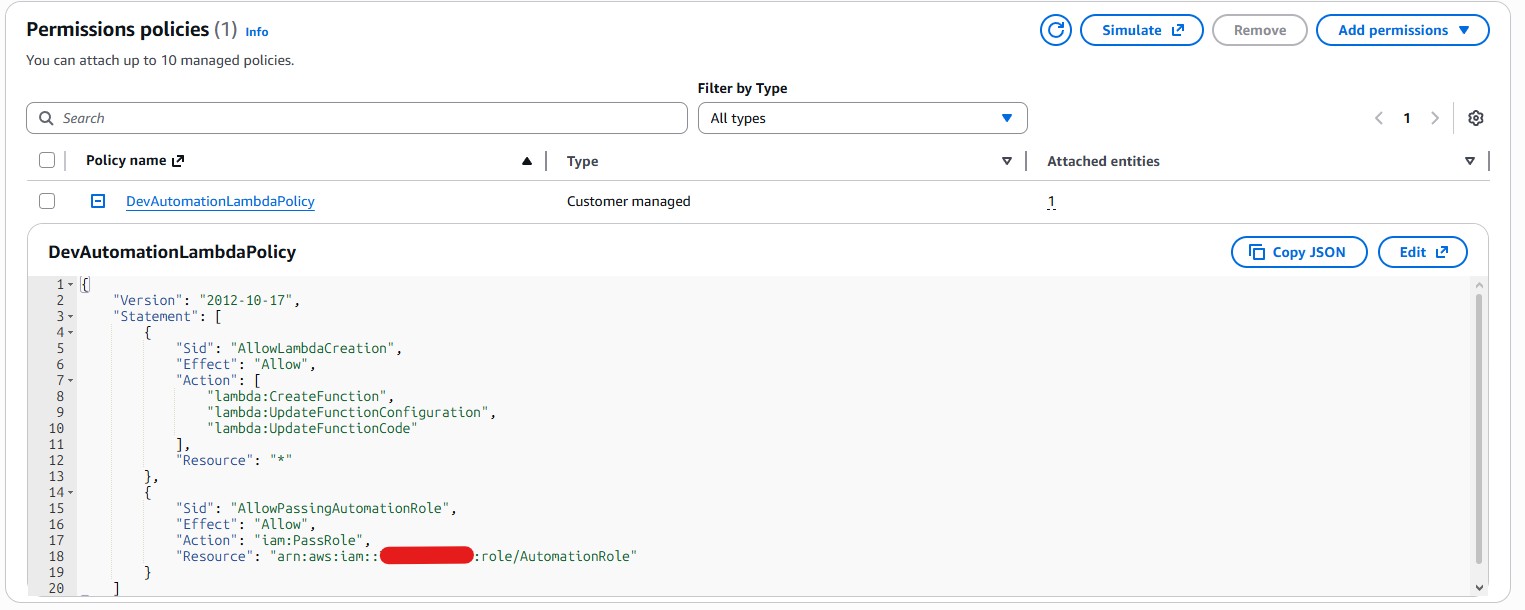
| dev-automation | Lambda automation experiments |
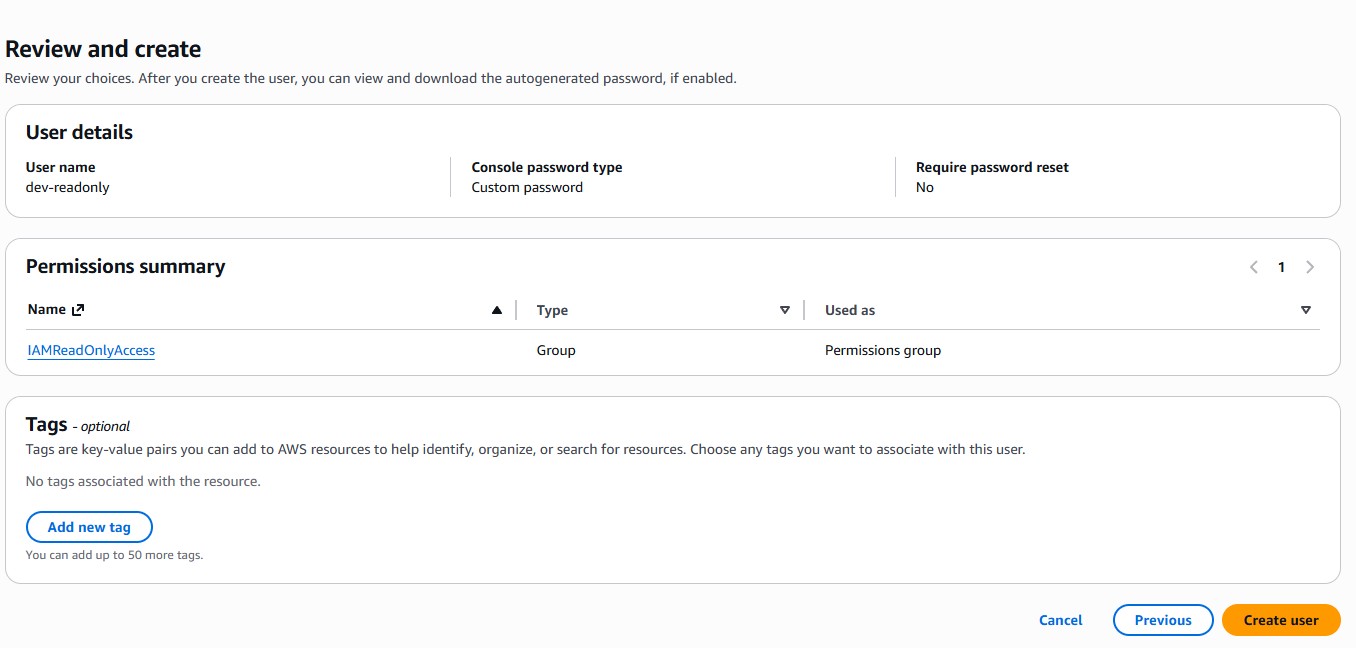
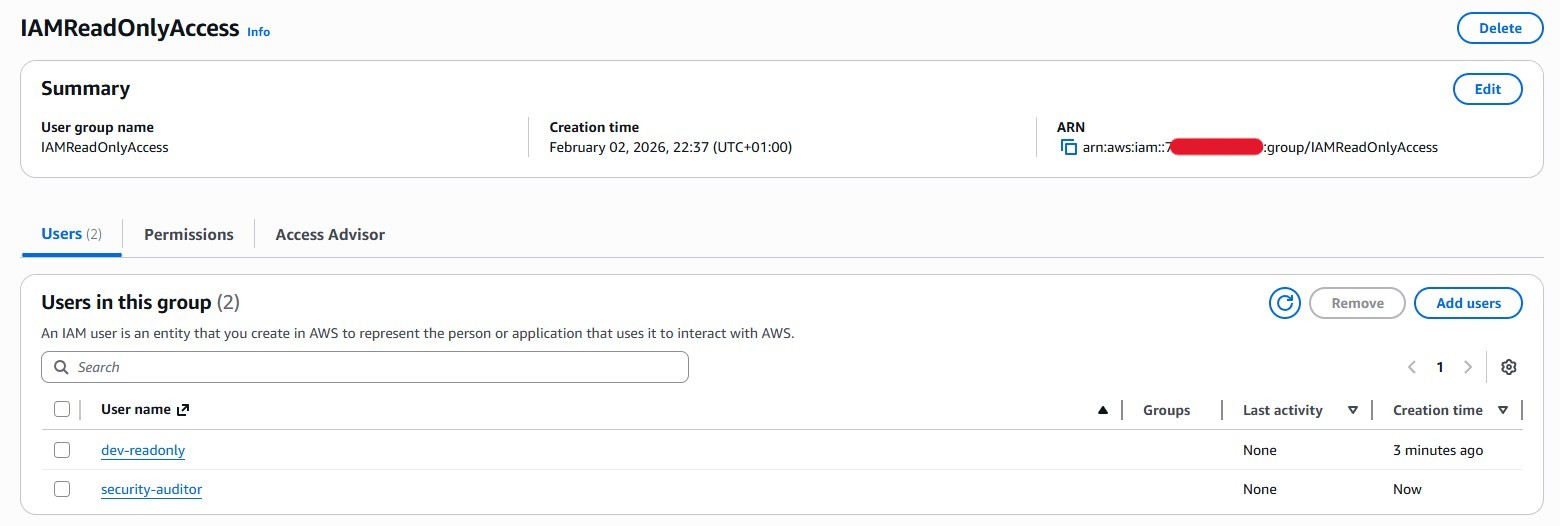
| dev-readonly / security-auditor | IAM read-only visibility |
| guest-contractor | Minimal / no permissions |
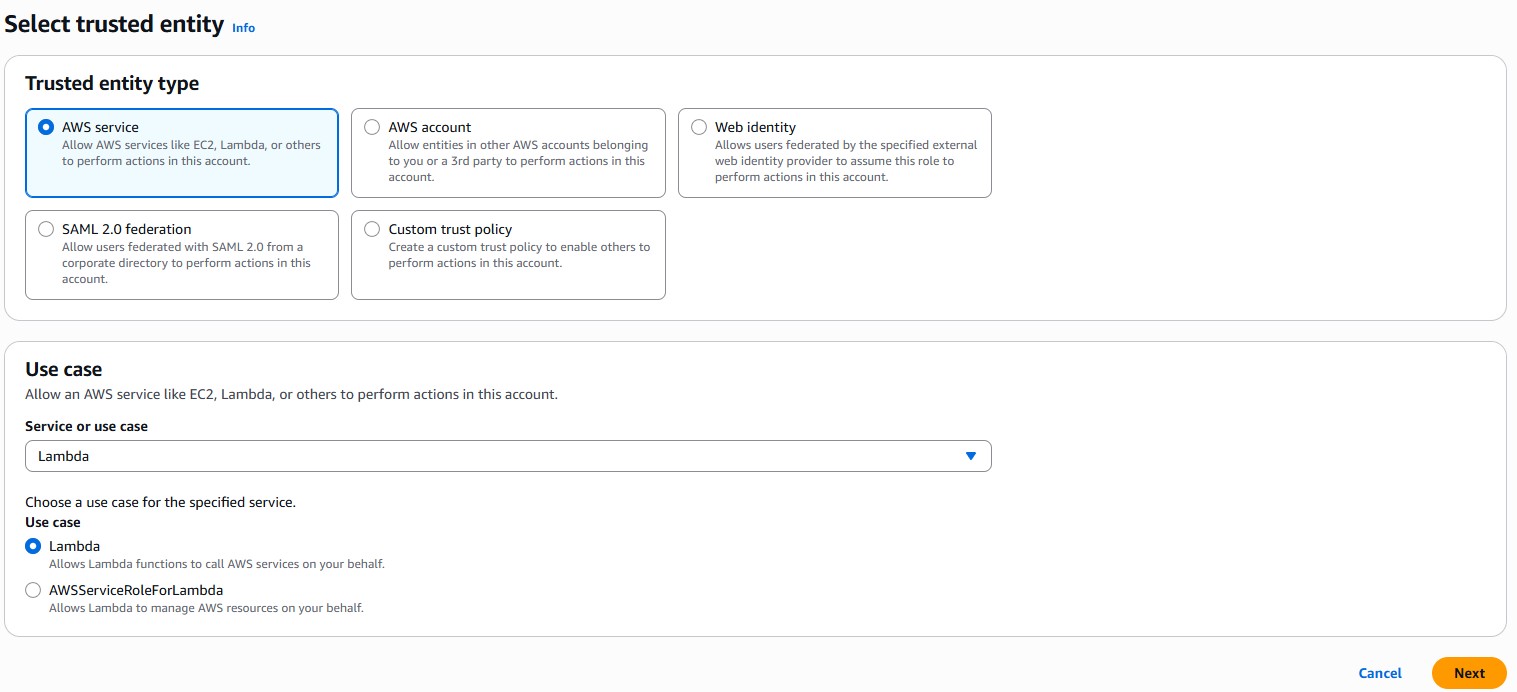
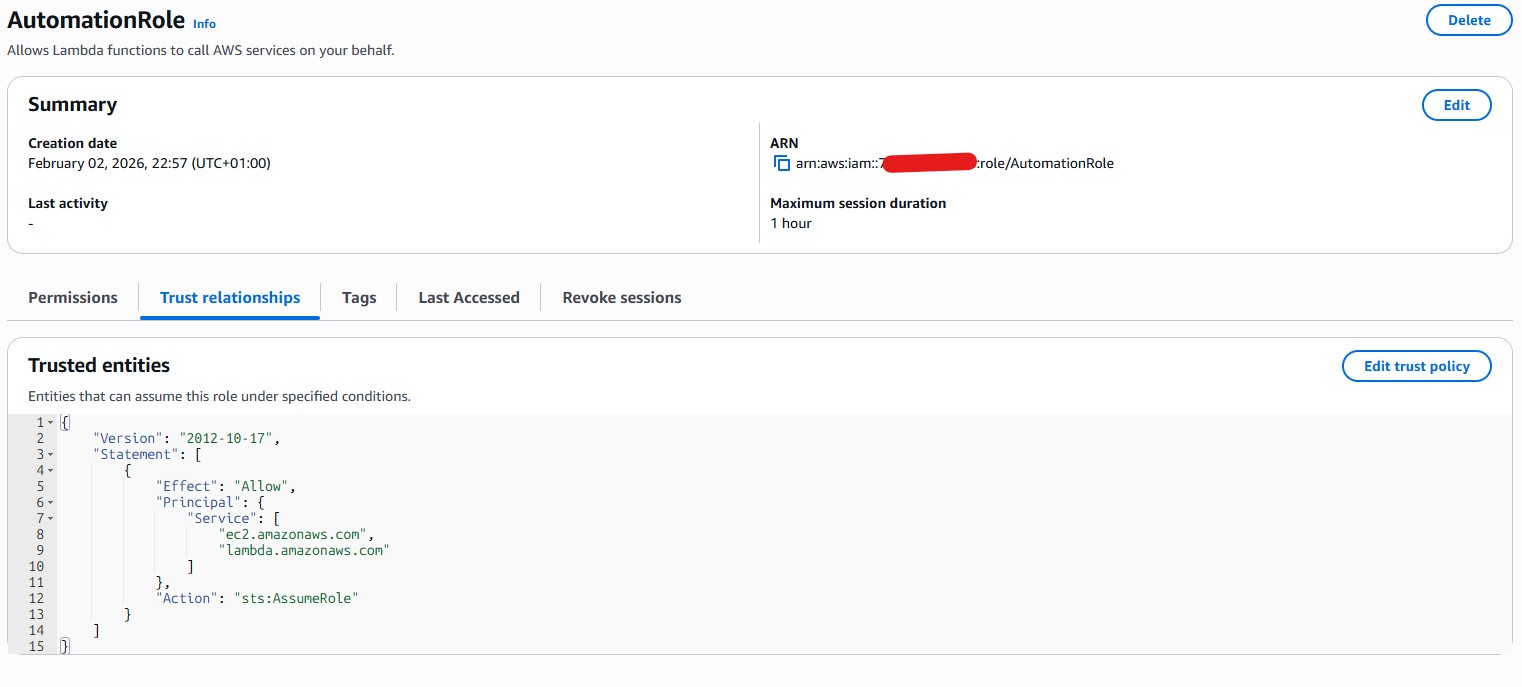
IAM Roles
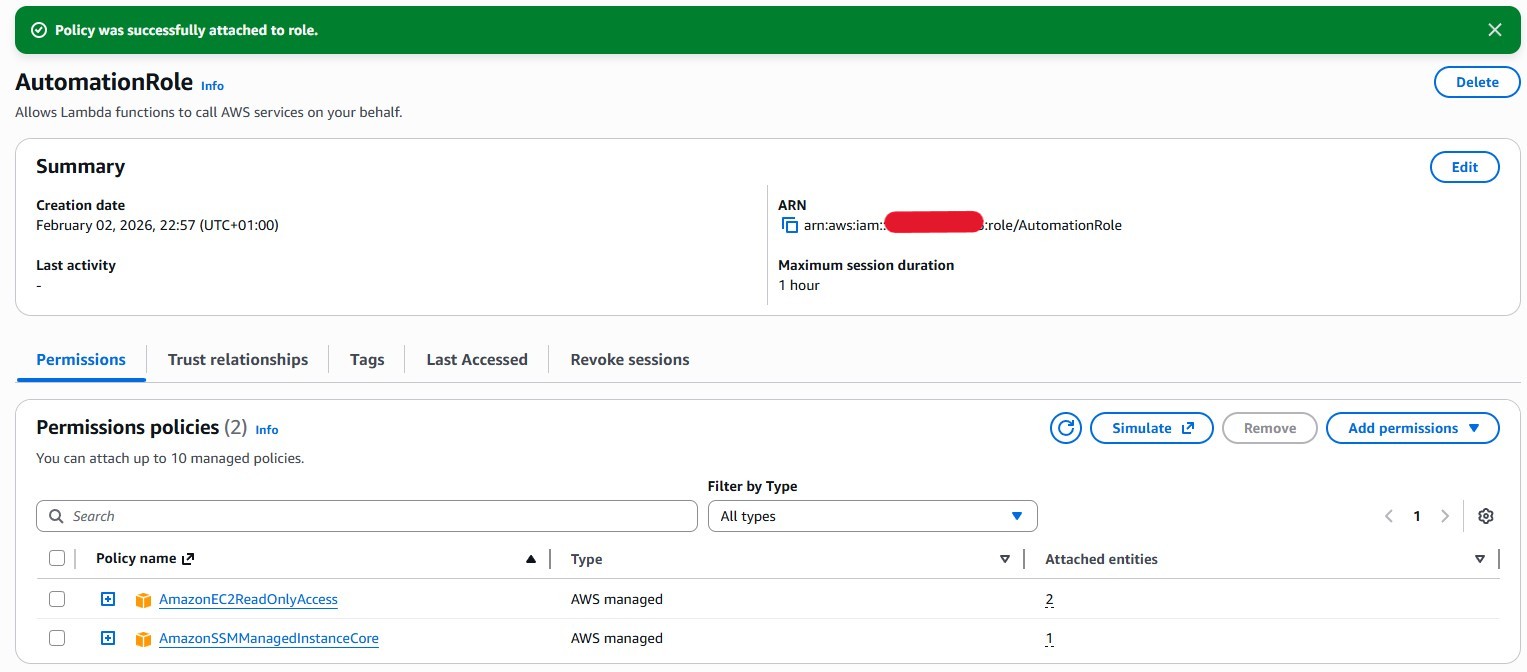
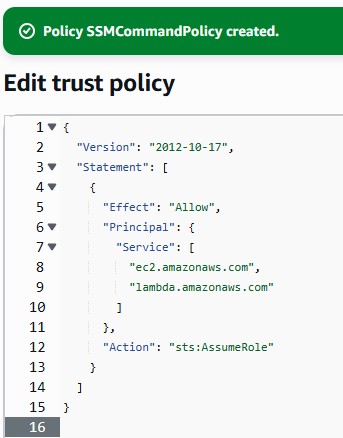
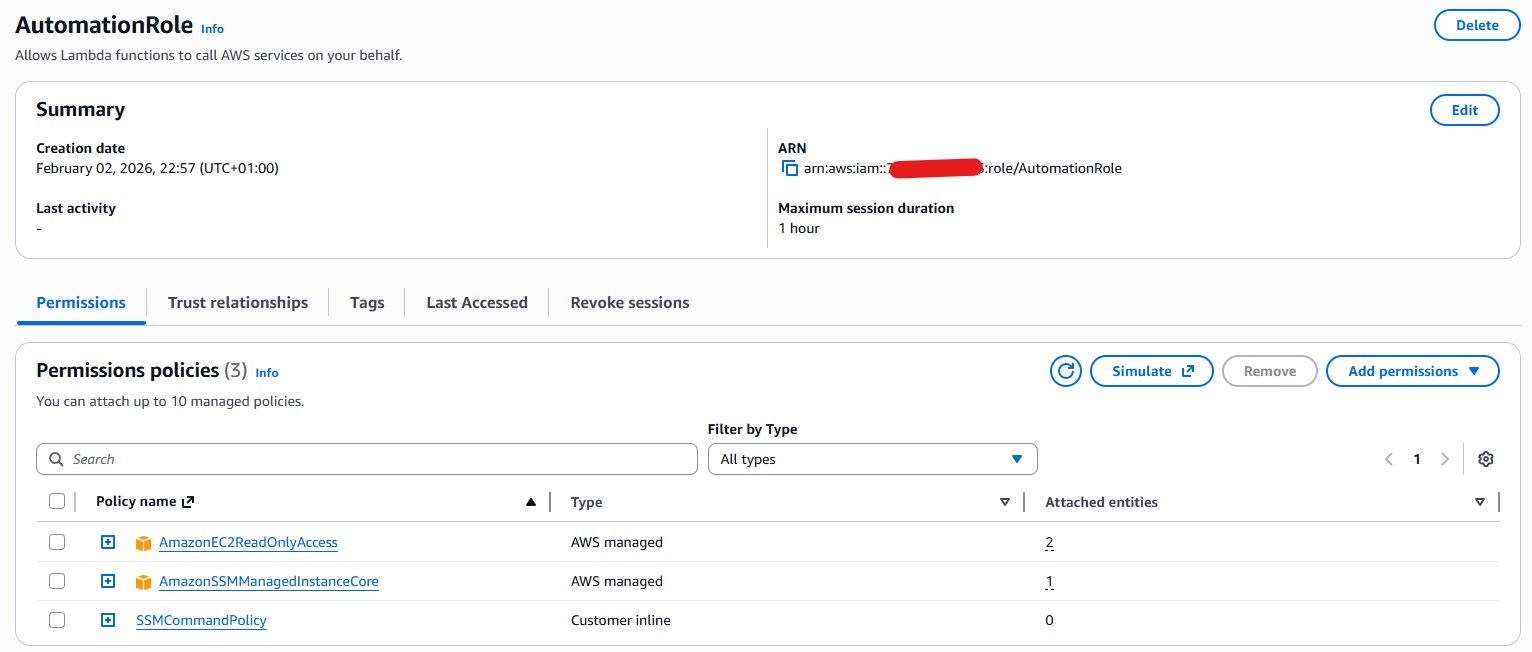
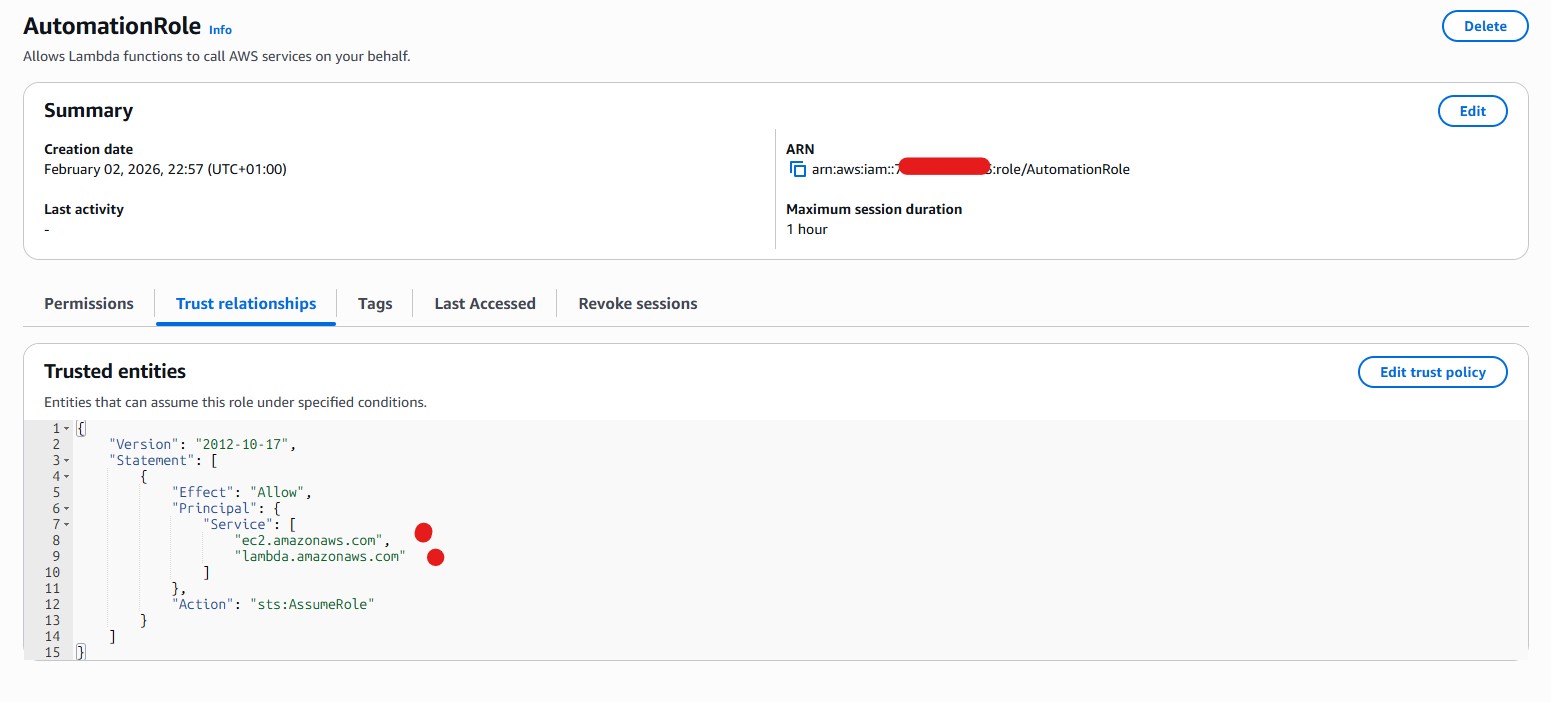
- AdminEC2Role: Trust
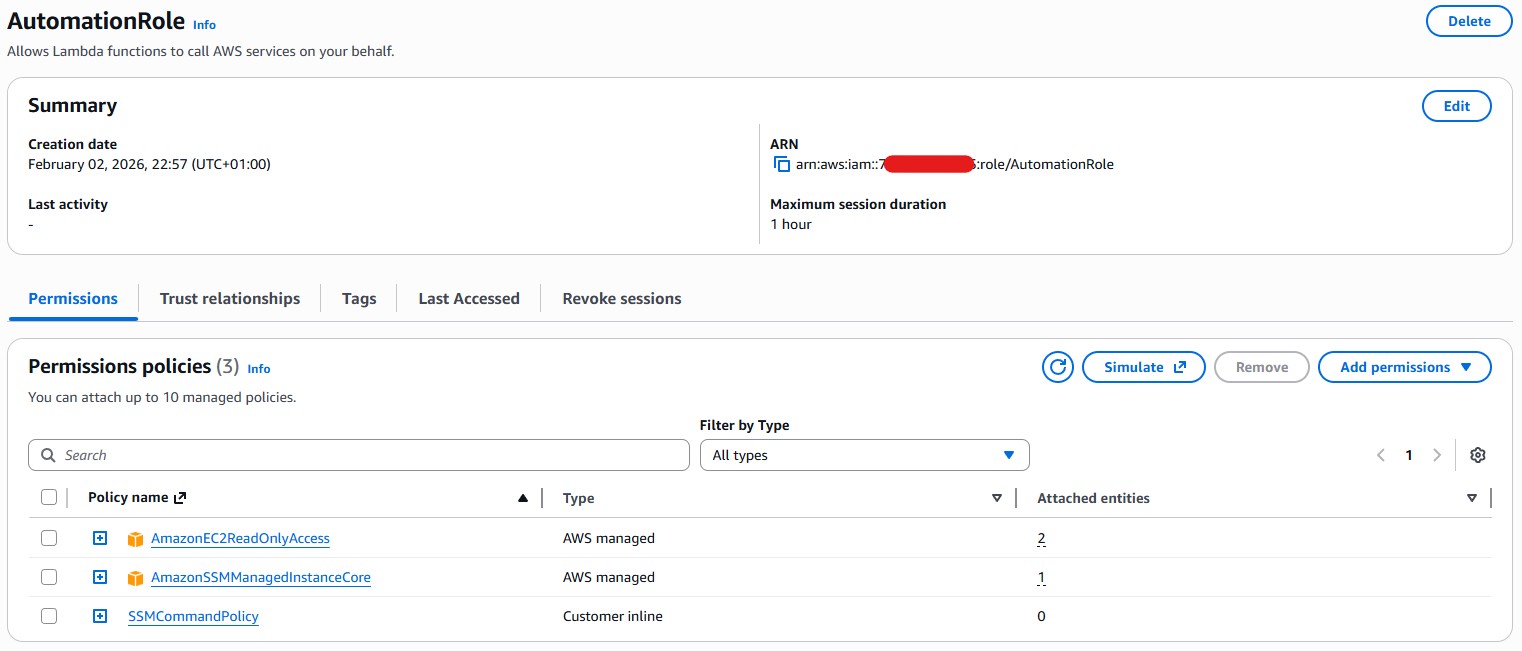
ec2.amazonaws.com, PolicyAdministratorAccess— high-risk role - AutomationRole: Trust
ec2.amazonaws.com,lambda.amazonaws.com, Policy EC2 + SSM — orphaned / over-trusted - ReadOnlyAuditRole: Trust IAM users in account, Policy
SecurityAudit
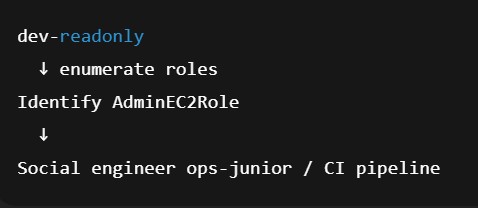
Context from LAB 2 — Social Engineering & Access Modeling
LAB 2 focused on human trust boundaries, not technical exploitation. Key observations:
- Junior staff relied on console visibility to judge safety
- Automation users were implicitly trusted
- Role names and infrastructure details were casually shared
- No malicious intent — only assumed trust
This laid the groundwork for LAB 3.
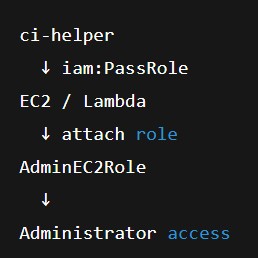
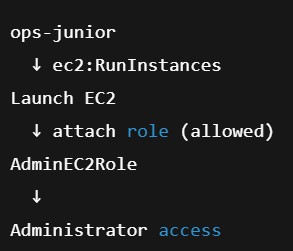
Threat Model
The attacker (ci-helper) did not possess full automation credentials or independent infrastructure design capability. Instead, the attacker relied on social engineering of a junior operations user to obtain a valid EC2 launch blueprint, including the AMI ID, instance type, region, and knowledge of a privileged IAM role.
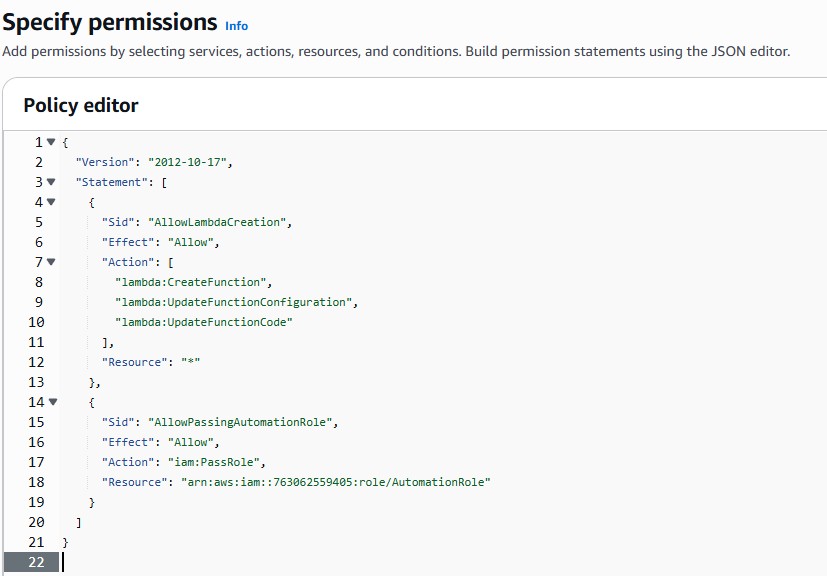
While console-based IAM controls prevented role discovery and selection, this human trust boundary bridged the remaining gaps. Once the attacker obtained a known-good configuration, iam:PassRole enabled privilege escalation through the AWS CLI without requiring any IAM visibility or administrative permissions.
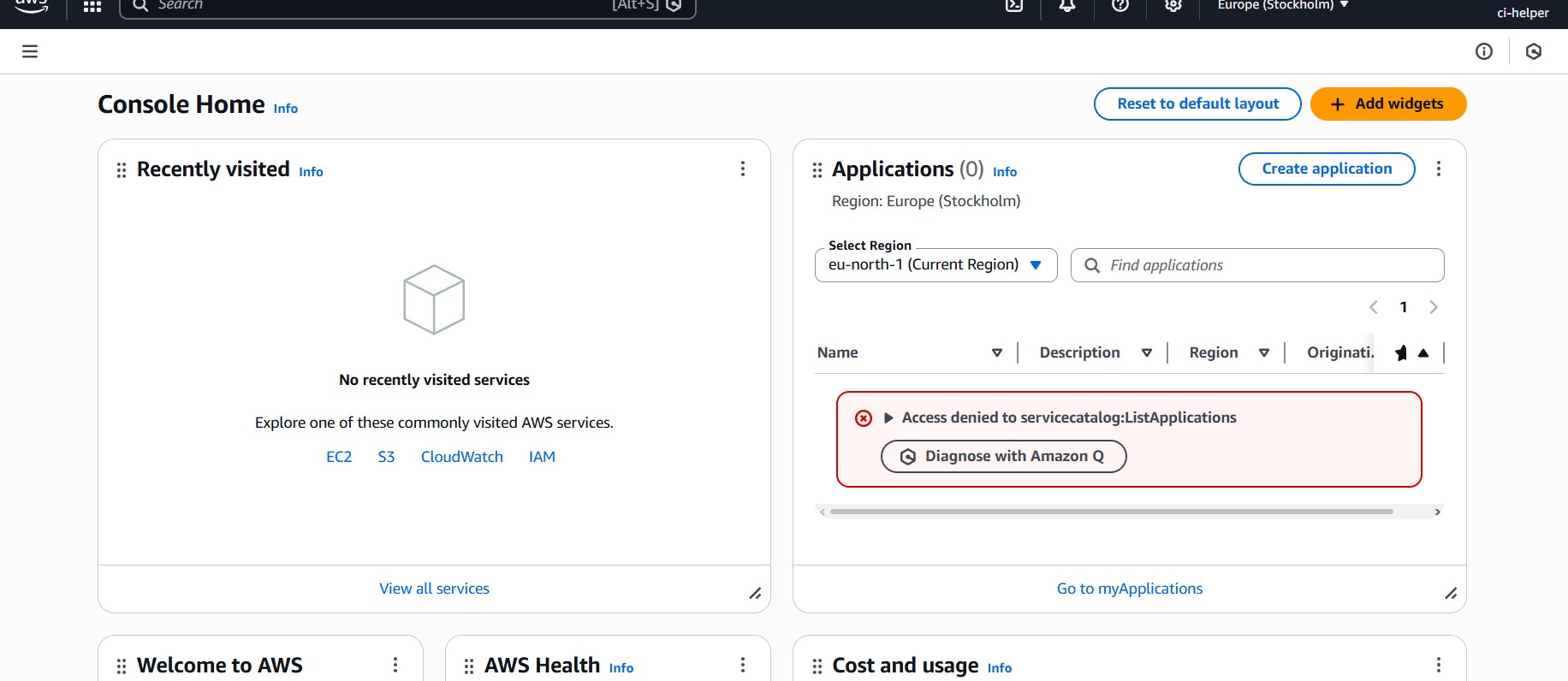
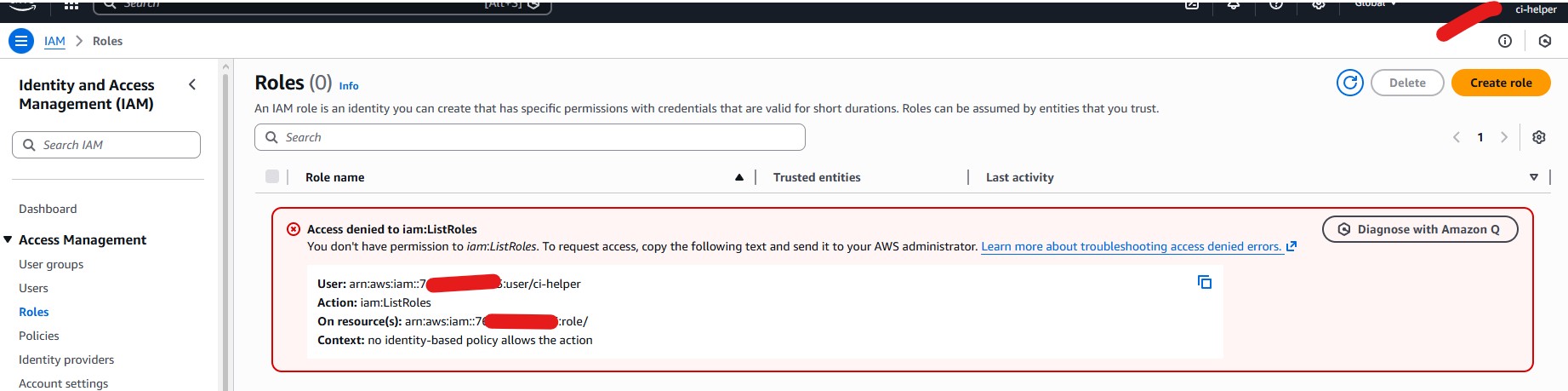
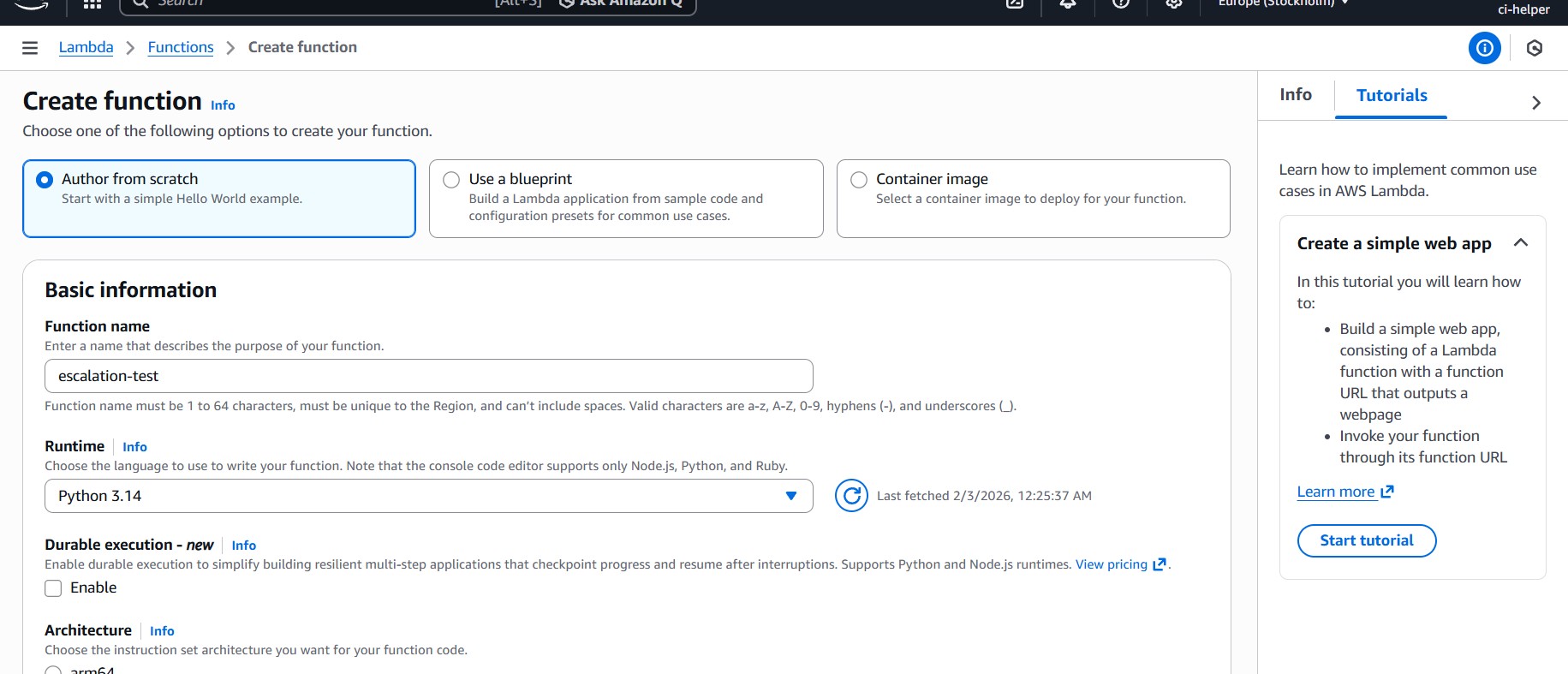
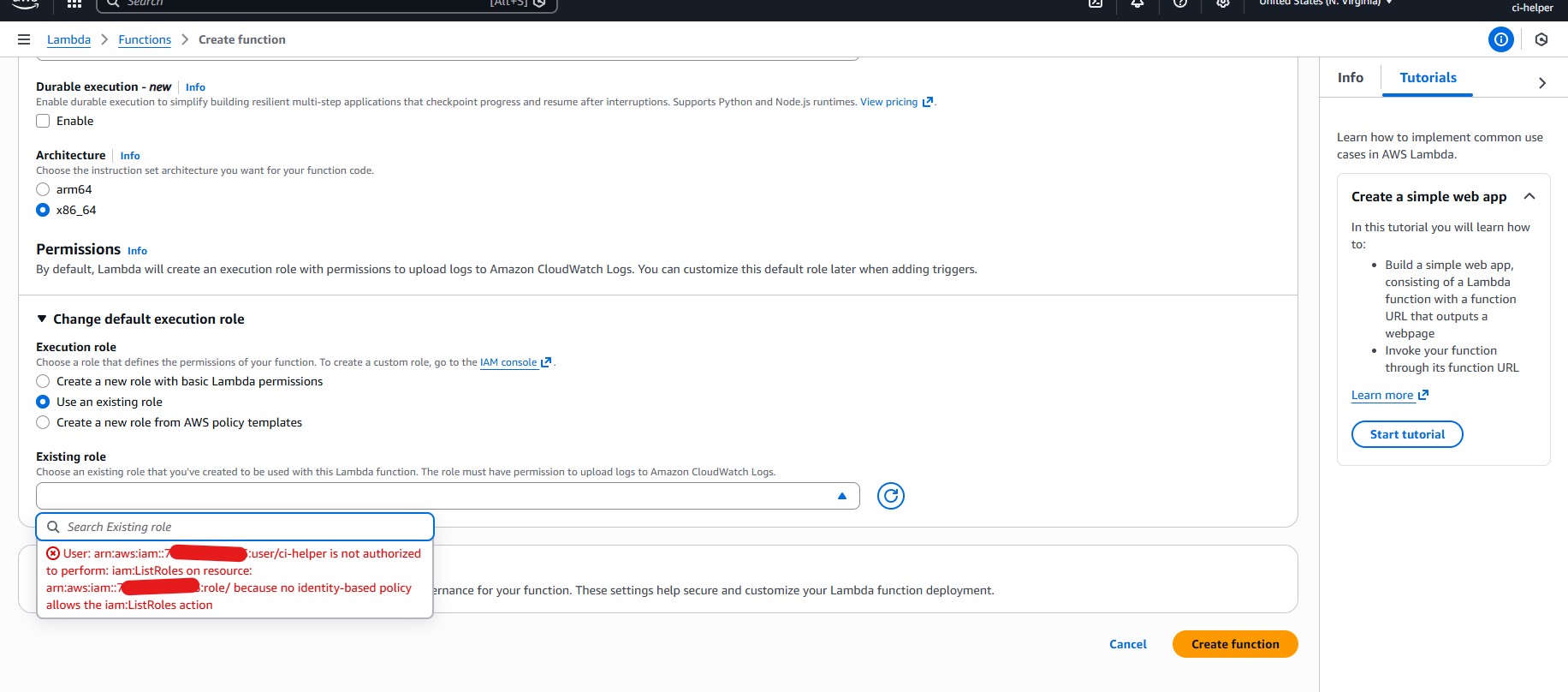
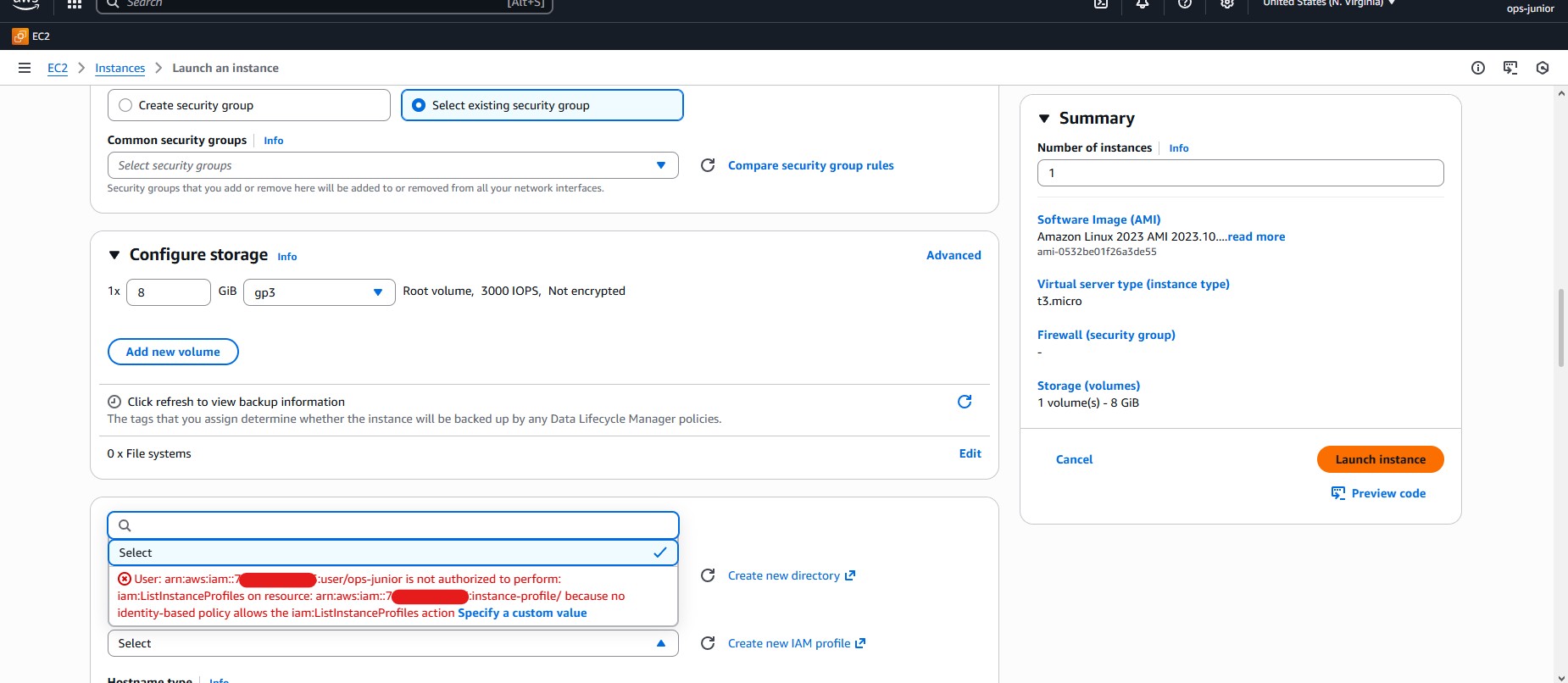
Phase 1 — Console-Based Escalation (Blocked)
Observed behavior:
iam:ListRoles,iam:ListPolicies→ AccessDenied- Lambda role dropdowns empty
- Role creation (
iam:CreateRole) denied - EC2 role selection restricted
Privilege escalation via PassRole was blocked at the console layer due to missing role enumeration permissions, demonstrating effective IAM hardening against browser‑based abuse.
Phase 2 — Initial EC2 Activity by ops‑junior (Console)
ops-juniorlaunched EC2 instances via console- Could not explicitly select
AdminEC2Role - Instances launched successfully
- This caused initial confusion about who launched which instance and whether instances were privileged
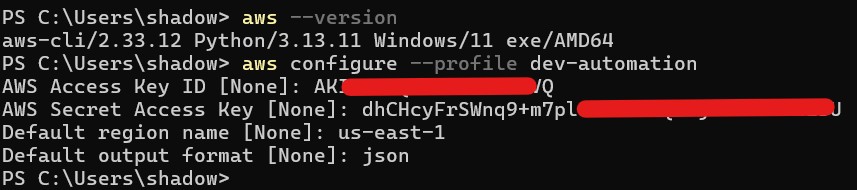
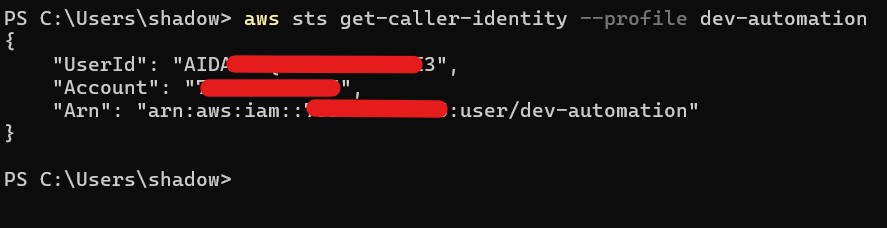
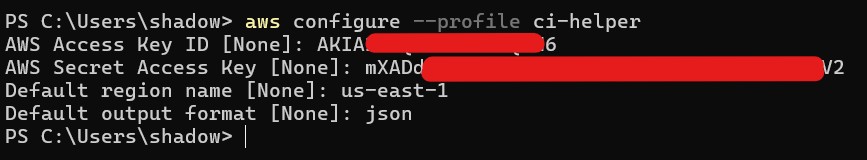
Phase 3 — Attacker Pivot to CLI (ci‑helper)
With console escalation blocked, ci-helper pivoted to AWS CLI (PowerShell) using existing automation access keys.
The attacker did not need role listing, IAM visibility, or role creation — only the name of a privileged role, iam:PassRole, and ec2:RunInstances.
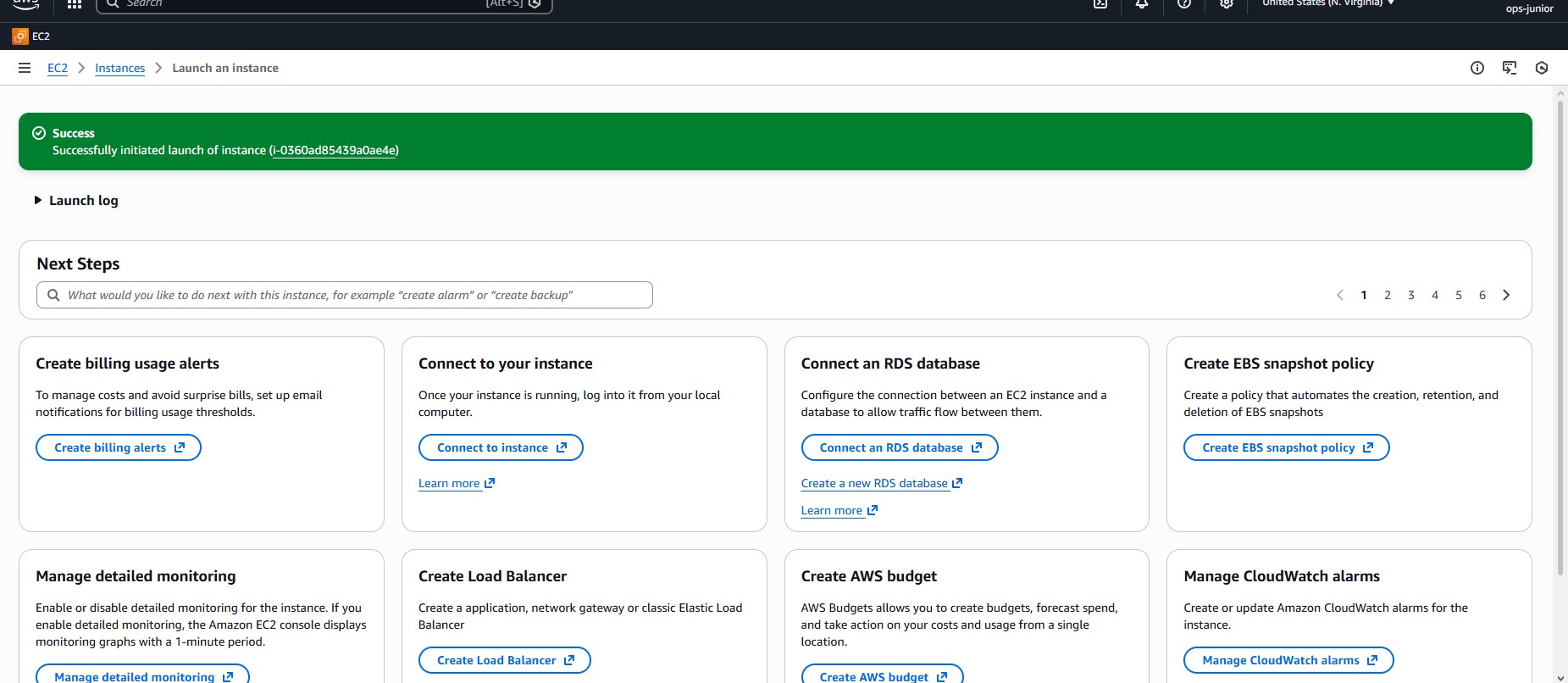
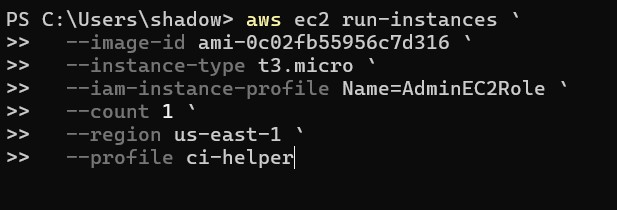
Phase 4 — CLI Exploitation (Confirmed Escalation)
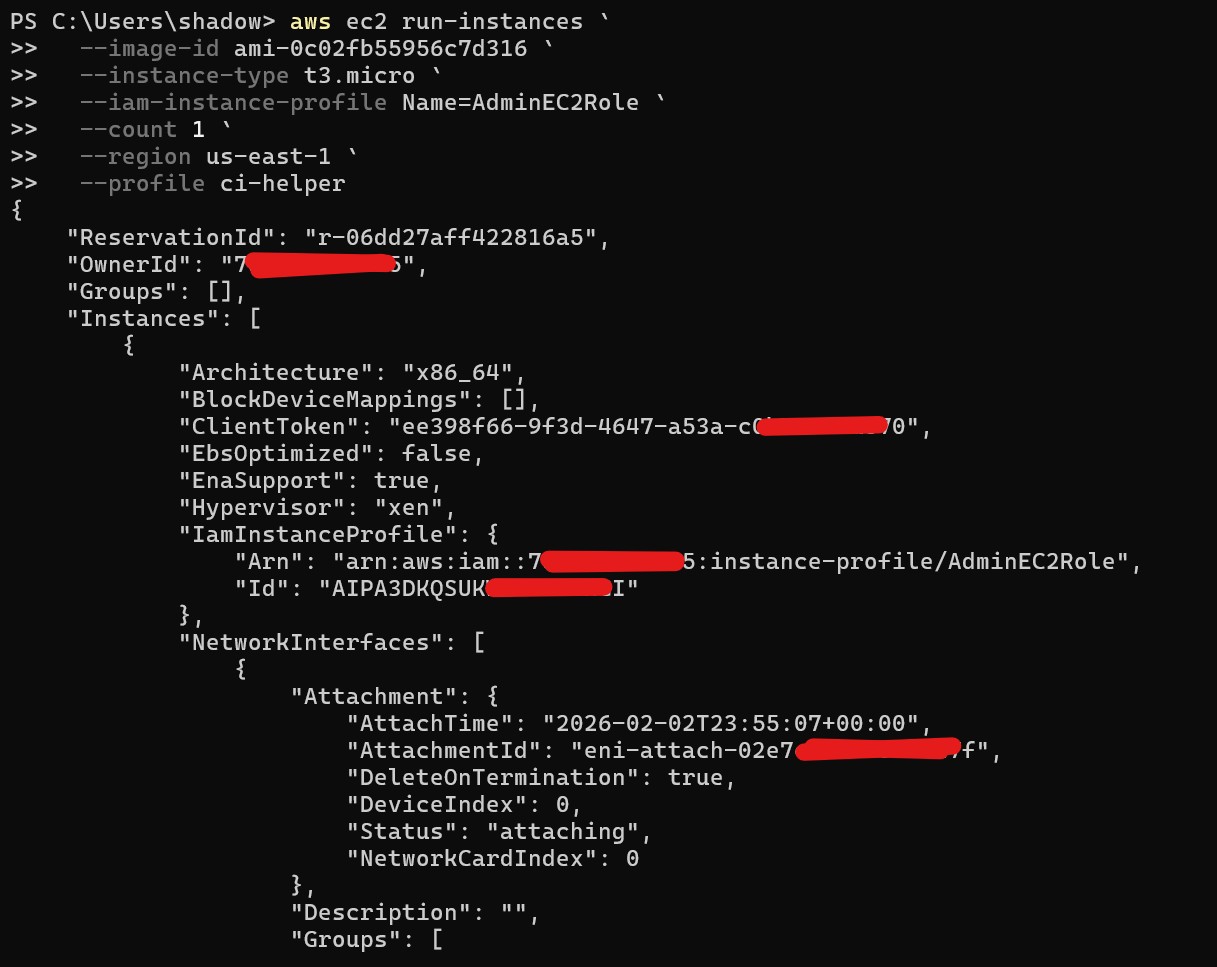
Command Executed (AWS CLI):
aws ec2 run-instances \
--image-id ami-0c02fb55956c7d316 \
--instance-type t3.micro \
--iam-instance-profile Name=AdminEC2Role \
--region us-east-1 \
--profile ci-helperResult:
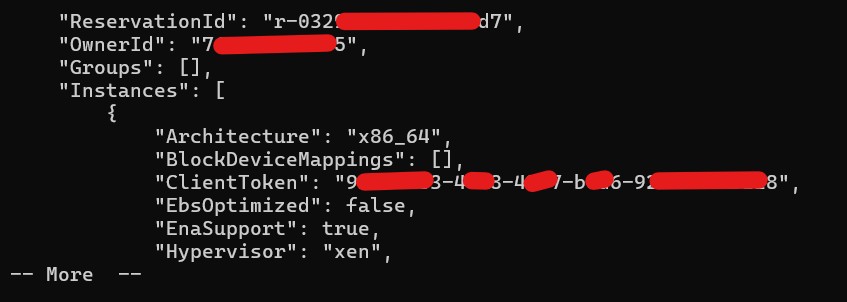
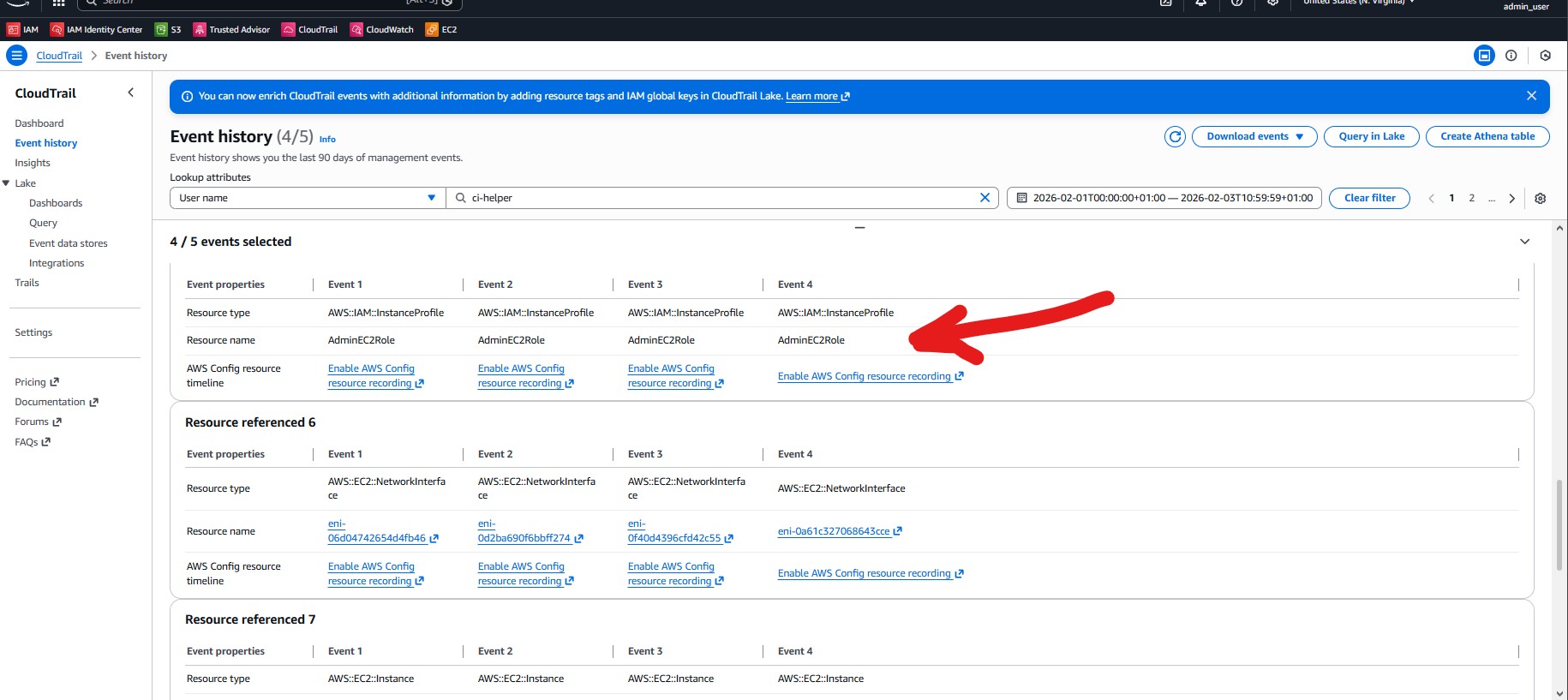
- EC2 instance launched successfully
AdminEC2Roleattached- Confirmed in CLI output:
"IamInstanceProfile": { "Arn": "arn:aws:iam::7xxxxxxxxxx5:instance-profile/AdminEC2Role" }
This proves that ci-helper, a non‑privileged user, socially engineered information to launch persistent administrator‑privileged EC2 infrastructure.
Phase 5 — Asymmetric Control (Critical Finding)
Despite creating the instance, ci-helper could NOT:
- Terminate the instance
- Modify it
- Enumerate EC2 resources
All lifecycle actions failed with AccessDenied.
ci-helper, a non‑privileged user, socially engineered information to launch persistent administrator‑privileged infrastructure, which they could not later manage. This is a serious operational and security risk.
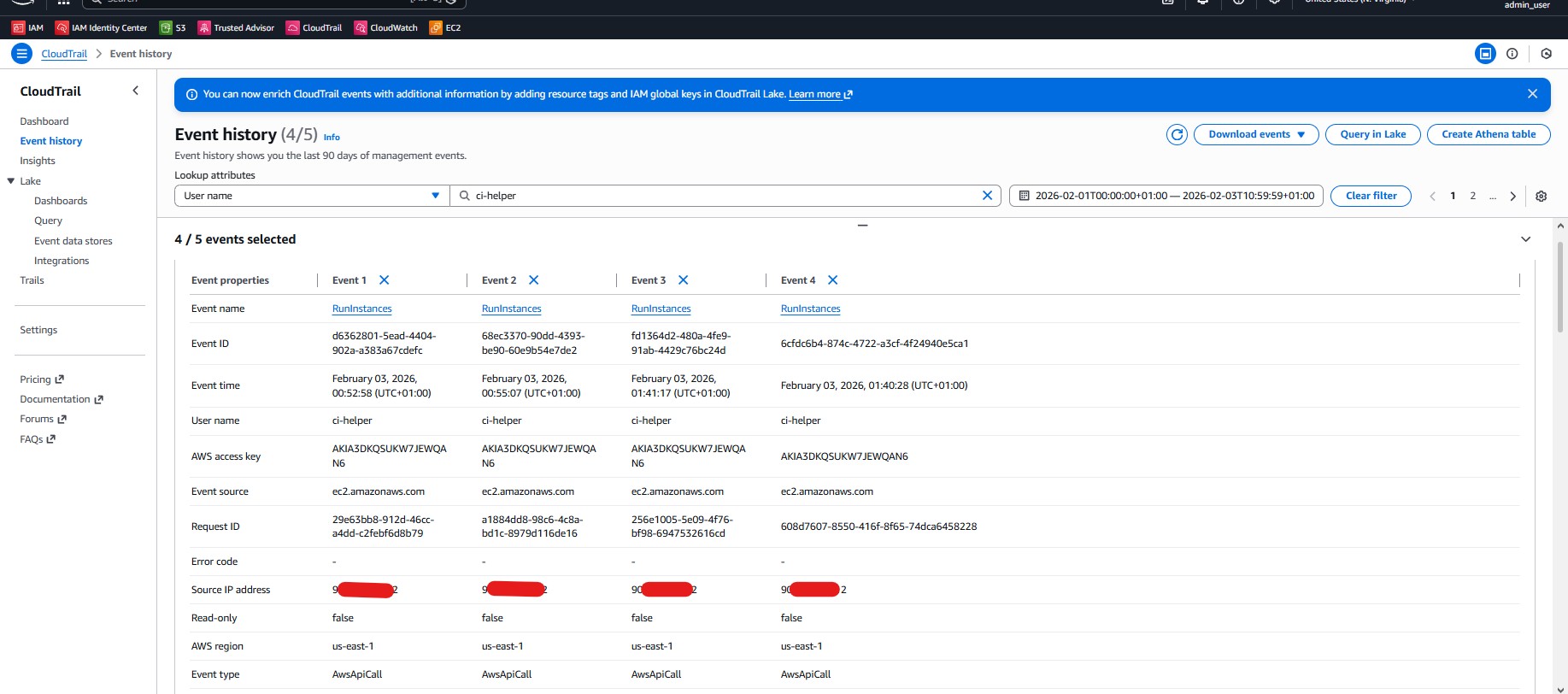
CloudTrail Verification
CloudTrail RunInstances events confirmed:
- Multiple launches by
ci-helper - Same source IP
- Same AMI
- Different timestamps
- Distinct access keys
AMI Clarification
ami-0c02fbxxxxxx7d316is a public Amazon Linux 2 AMI- AMIs are templates, not instances
- The same AMI can launch unlimited unrelated EC2 instances
Privilege escalation occurred via role attachment, not AMI reuse.
Security Impact Analysis
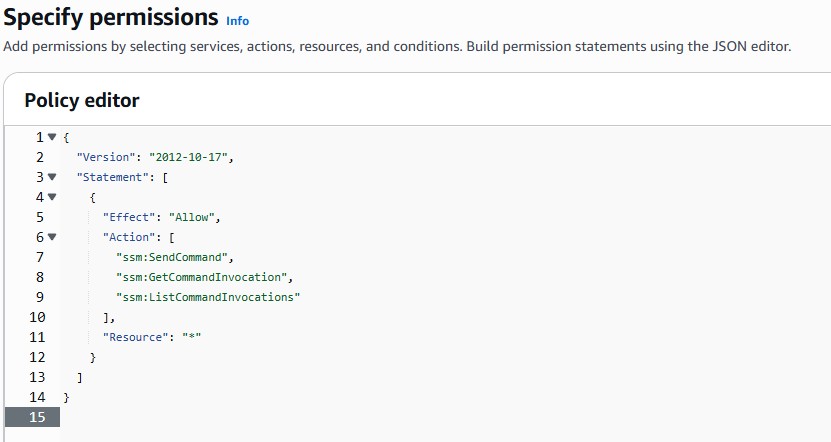
What Went Wrong
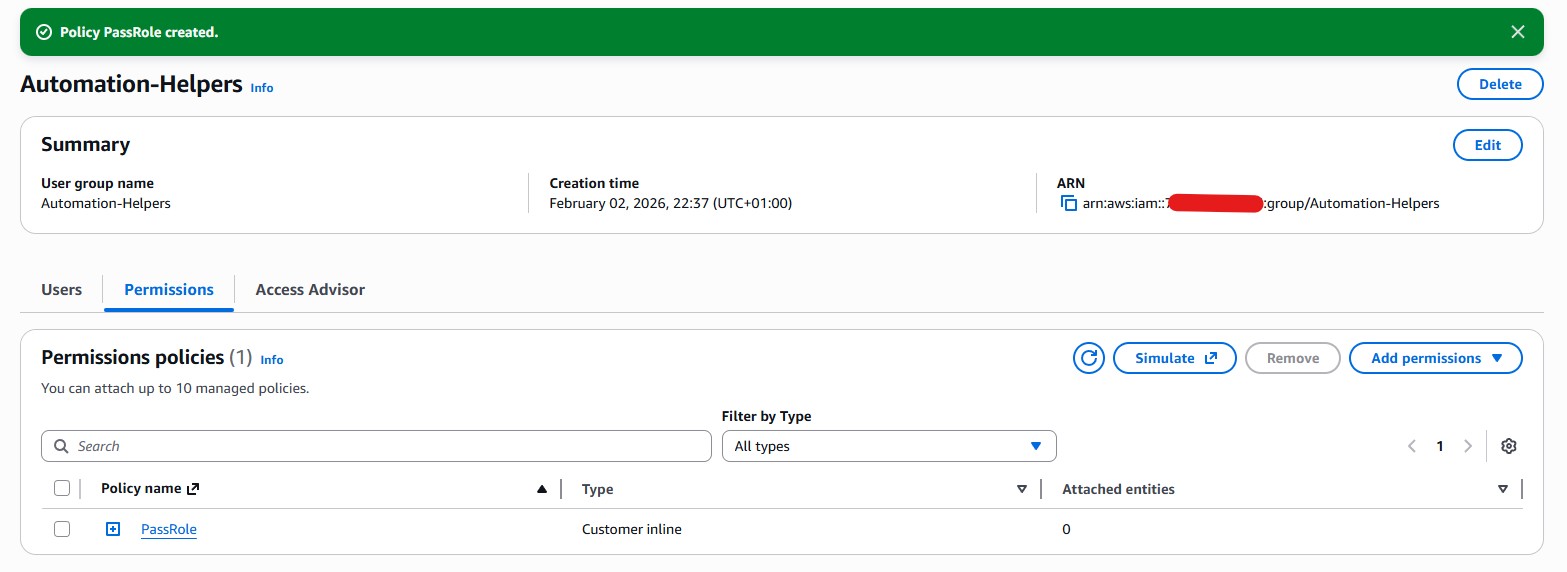
iam:PassRolegranted without sufficient constraints- No
iam:PassedToServicerestriction - Automation permissions exceeded lifecycle permissions
- Role name secrecy relied on as a control
What Went Right
- Console hardening blocked browser‑based abuse
- IAM listing restrictions slowed discovery
- Admin intervention successfully contained impact
Key Lessons Learned
iam:PassRoleis privilege escalation when combined with compute- Console protections ≠ API protections
- Role name secrecy is not a security boundary
- Automation users are high‑risk principals
- Creation permissions must align with lifecycle permissions
Defensive Recommendations
- Restrict
iam:PassRolewith explicit role ARNs andiam:PassedToService - Align
RunInstanceswithTerminateInstances - Monitor CloudTrail for
PassRole+RunInstances - Treat CI/CD credentials as privileged assets
- Periodically audit orphaned and over‑trusted roles
Final Conclusion
Even when IAM role visibility, listing, and creation are restricted, a user with iam:PassRole and workload execution permissions can escalate privileges through automation interfaces. Console‑based guardrails do not prevent CLI‑based role abuse.
This lab demonstrates a realistic, defensible, and commonly overlooked AWS privilege escalation path, combining technical misconfiguration with human trust failures — exactly how real incidents occur.